

Organizations are increasingly embarking on digital transformation journeys. The transformation is enabling them to keep pace with the competition, optimize IT asset security, and meet evolving user expectations. It is helping enterprises sustain and maintain their diversified IT infrastructure. However, the widening IT landscape, an accelerated shift toward the cloud, and the increased adoption of collaboration applications and tools are also blurring network perimeters.
The attack surface has expanded. Cybercriminals are finding it easy to access enterprise networks and execute cyberattacks. Infusing security into every phase of digital transformation projects, with added focus on code security, is becoming extremely important.

Digital transformation can include a series of activities to support an organization’s objectives and growth. Enterprises aim to update legacy applications, digitize their data and assets, move on-premises applications to the cloud, and harness the power of disruptive technologies as part of the transformation.
Organizations are leveraging the potential of artificial intelligence, deep learning, the Internet of things (IoT), no-code or low-code platforms, and data analytics in their functions and applications. They are rethinking their operations models, processes, and applications.
According to a Forrester survey, up to 93% of enterprises believe that ground-breaking technologies are an essential element for the success of digital transformation initiatives. But what do enterprise leaders aim to achieve by investing in innovation projects, new technologies, and digital transformation?
New and emerging technologies such as robotic process automation (RPA) allow teams to automate processes. Automation reduces manual intervention and human error, thereby improving accuracy and operational efficiency. New technologies also offer the means to predict and assess risks accurately before application release. So, only the best-performing versions of applications reach users.
In the present highly competitive environment, enterprises are doing all they can to retain existing users as well as win new customers. To meet evolving customer expectations, they need to continuously update their portfolios with new applications and services. Digital transformation has moved from being just desirable to a necessity. Newer working models such as development operations (DevOps) and agile delivery are enabling teams to identify and address issues and bugs at an early stage in the software supply chain. Teams can deliver high-quality products and applications faster by addressing challenges proactively.
The remote work model and dissolving network perimeters have led to an increase in phishing attacks, malware installations, ransomware attacks, and other cybercrimes. Quite a few enterprises have realized the need to decrease security exposure and bring down cybersecurity-related disruptions. However, many are yet to take up digital transformation initiatives focused on improving security and compliance. Teams must ensure applications and systems are always secure, up-to-date, and compliant. To develop and transform digital assets such as enterprise applications, websites, databases, and cloud servers, enterprise leaders are promoting a DevOps culture across the organization. But on its own, the approach is not enough anymore. Today, digital security is considered the backbone of digital transformation. It is time every enterprise incorporated cybersecurity in their DevOps and continuous integration and continuous delivery (CI/CD) processes.
The Importance of Cyber Protection in Digital Transformation
The move toward the cloud and newer digital technologies is reducing time-to-market for new products and services. Stable code is considered obsolete in an era of open-source, cross-platform, and back-end JavaScript runtime environments. However, newly introduced technologies and third-party code used in digital transformation initiatives are also exposing organizations, their data, digital infrastructure, and IT assets to cyber risks. The pressure to innovate rapidly is placing security on the back-burner.
Security can pose as a bottleneck in a high-velocity DevOps environment. Additionally, new technologies integrated as part of digital transformation can present new security threats to enterprise applications and systems. As the number of digital transactions increases, the volume of data transmitted, stored, and managed is also increasing. Cybercriminals will take advantage of vulnerabilities in the organization’s expanded digital landscape to steal and misuse crucial and sensitive data.
If cybersecurity is not included in digital transformation initiatives, organizations can fall prey to cyberattacks and data breaches. Traditional security controls are not enough to identify, monitor, and mitigate present-day cyberattacks. Organizations must strengthen their security posture with automated solutions that work continuously in the back-end, detecting and mitigating cyber risks.
Before embarking on the digital transformation journey, organizations must:
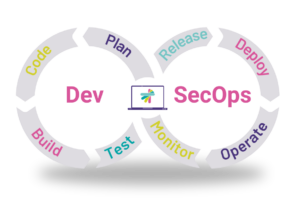
Quite a few teams have adopted agile and DevOps approaches. They are able to release applications and code updates faster than ever before. However, they still grapple with security challenges after go-live. This is because they consider security as an isolated domain. DevSecOps can address the issue.
The first step toward becoming a truly digital organization is to embrace a culture of security and follow a DevSecOps approach across every team and process. In DevSecOps architecture, security is at the core of every software development and IT operations process. With the help of technology solutions such as Kiuwan Code Security, teams can ensure applications they build are secure right from the start.
With DevSecOps, security is prioritized and continuously infused into every stage in the software development lifecycle (SDLC). The approach offers several advantages.
Kiuwan offers two key products, Kiuwan Code Security and Kiuwan Insights Open Source, as well as useful add-ons to support digital transformation. The solutions allow quick code scans to identify vulnerabilities — accurate results are generated within minutes. They easily integrate into organizations’ CI/CD and DevOps pipelines and facilitate security automation.
The Kiuwan Code Security solution for static application security testing (SAST) enables developers to validate security at every step in the DevOps pipeline. They can easily and effectively detect bugs with automated code scanning. The solution adheres to even the most stringent security standards, including OWASP and CWE, supporting safe digital transformation.
With Kiuwan Code Security, enterprises and developers are equipped with powerful tools to ensure code security. They can:
• Carry out penetration testing and “what if” simulations of various scenarios to proactively detect vulnerabilities
• Detect a range of code security issues, including uninitialized variables, misconfigured applications, credential or session prediction, cross-site request forgery, information leakage, inadequate transport layer and binary protection, cross-site scripting, and injection attacks
• Build secure applications easily. Kiuwan takes care of security requirements, suggesting what developers must focus on and to what extent, and even pinpointing the line of code level on which they need to act.
• Pick and choose from an extensive library of coding rules to meet their unique security requirements
• Monitor goals and always stay on track with the solution’s visual dashboard
• Automatically develop action plans to fix relevant security loopholes with customized industry-standard security-ranking-based reports
• Integrate application security into the integrated development environment (IDE) and evaluate security challenges directly from the IDE
• Easily integrate the solution with popular IDEs, build systems, bug trackers, and repositories
Developers often utilize third-party components in their digital transformation projects. Kiuwan Insights Open Source is a software composition analysis (SCA) solution helping developers mitigate risks from open-source and third-party components. It enables teams to address security bugs and challenges as well as comply with license requirements.
Kiuwan supports simple open-source code validation and risk management. Developers can:

Kiuwan Code Security and Kiuwan Insights Open Source support enterprises’ digital transformation initiatives and are available with flexible licensing options. Based on their requirements, teams can leverage the solutions for one-time scans or continuous scanning. Over 20,000 users across the world rely on Kiuwan to take care of their application code security.
Request a free demo now to see how the Kiuwan SAST and SCA products facilitate expediency in the development process and accelerate digital transformation.


