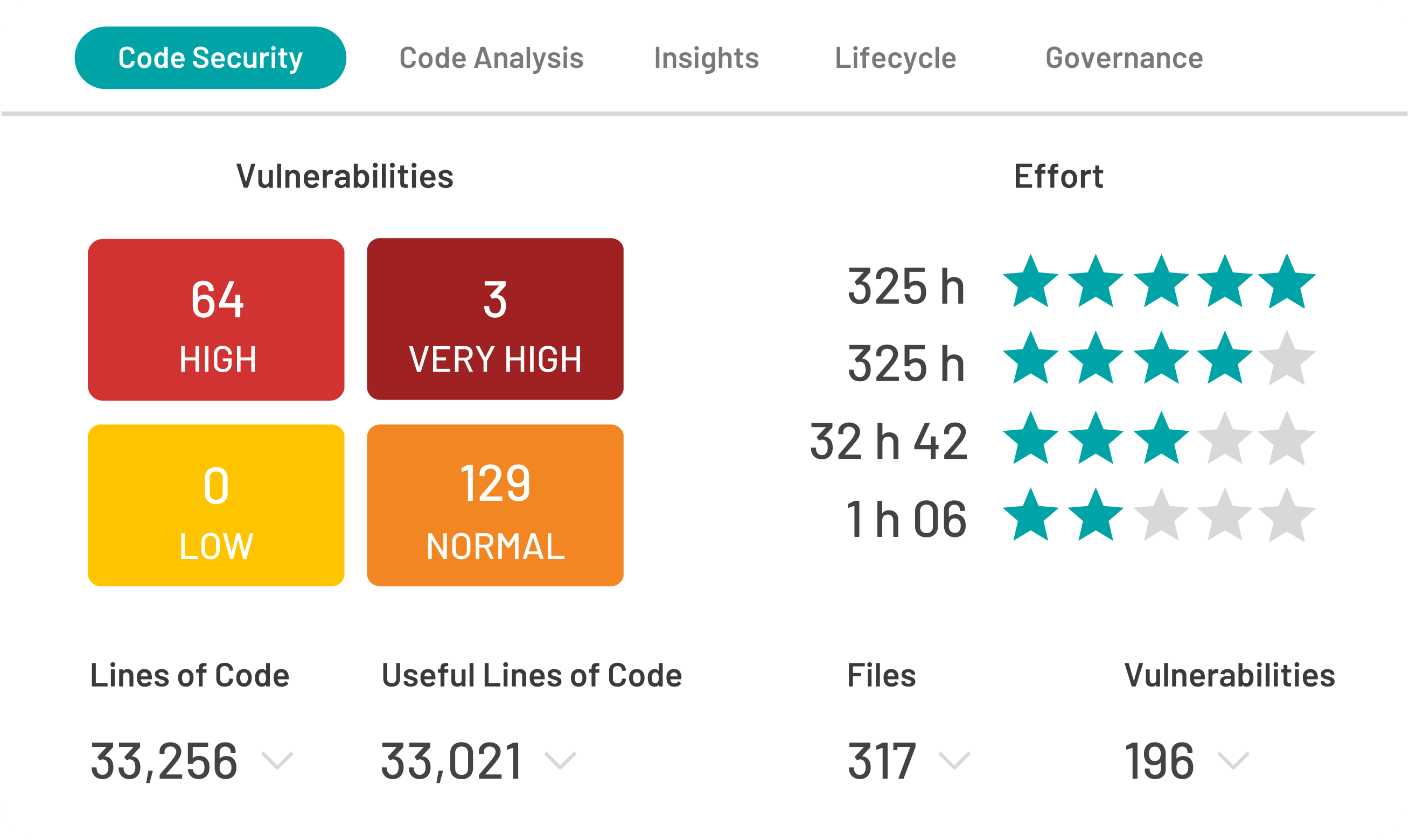
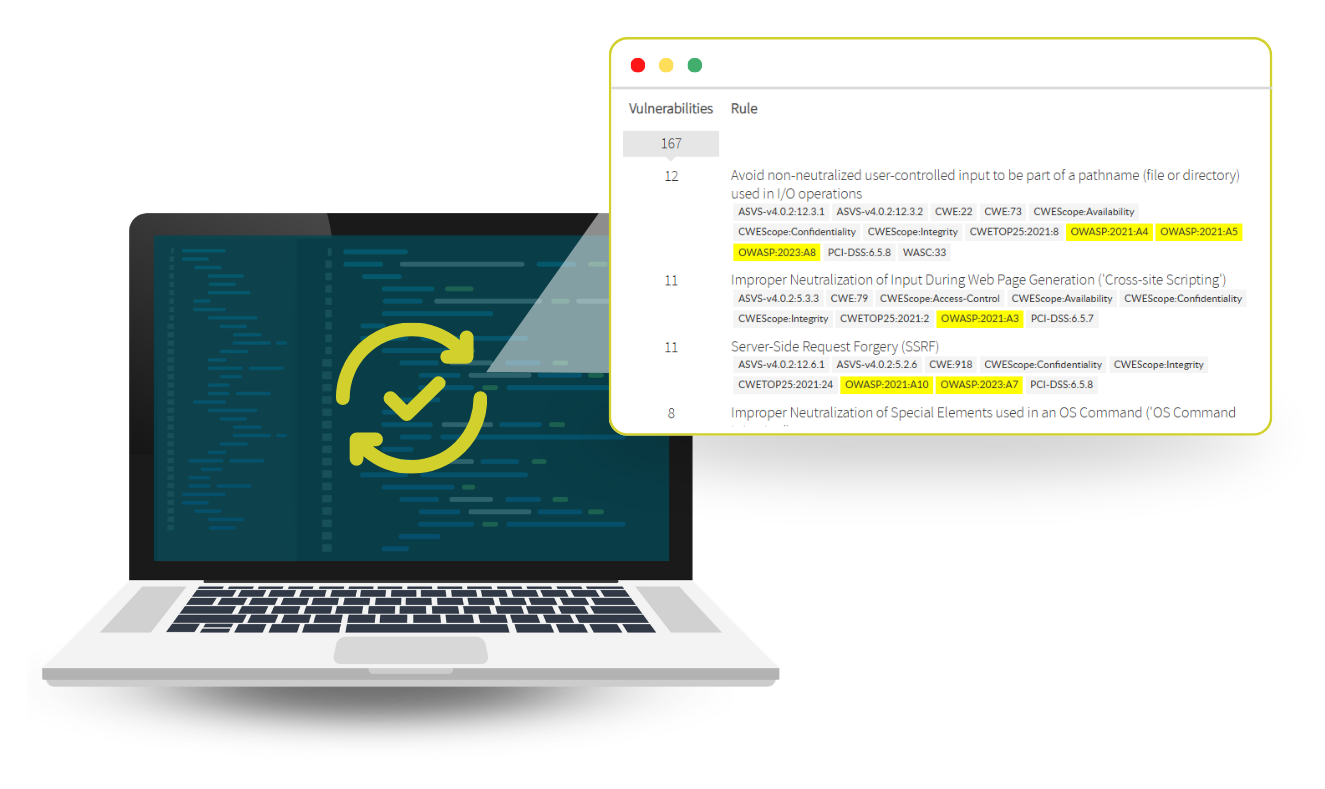
Kiuwan Code Security helps you detect and prioritize security vulnerabilities in source code early using static analysis. Run scans locally or in CI/CD, then review findings in a dashboard with remediation tips and compliance mappings.


Kiuwan Code Security’s user-friendly interface makes the dashboard very easy to use. We are highly satisfied with the findings from the code scans and the reporting capabilities. One of the reasons we chose Kiuwan is its strong focus on confidentiality. We are also very pleased with customer relations and after-sales support.