Kiuwan's Frequently Asked Questions
General information
Scanning your code
Technical questions
In both cases, all companies have similar needs:
- To detect security vulnerabilities early and fix them before deploying;
- To reduce the number of bugs affecting the performance and efficiency of their software;
- To manage the costs associated with development and maintenance properly;
- To gain greater control of their application development.
The Kiuwan applications can address all the above needs, regardless of the size and level of complexity of the development process.
- CIOs (Chief Information Officers) who need to make strategic decisions to improve software development
- CSOs (Chief Security Officers) who need to tackle security from the application perspective
- QA Managers and Engineers who need to control and monitor the quality state of applications under development
- Project Managers who need to know the health of the projects they manage from a technical perspective
- Application Architects who can discover structural flaws early in the development process
- Operation Officers who need to know the level of quality and security of the application they have in production
- Integration and Deployment Managers who need to make sure the structural and technical health of the applications they are moving in their respective pipelines is what is expected in the next environment
- Developers who want to develop the best software possible and learn as much as possible in the process
It complies with the most stringent security standards and covers all important programming languages. It is a cloud-based solution but offers the possibility of analyzing your source code locally.
Continuous subscriptions also include an IDE plugin to help developers work more efficiently.
Learn more about it on our here.
It also helps you ensure compliance with open source and copyleft licenses.
Learn more about it on our here.
- Kiuwan Code Analysis
The focus of this application is to reduce technical debt, making your code more maintainable, reliable, portable and efficient. - Kiuwan Governance
This is a business-oriented dashboard to help managers make smart decisions over their application portfolio. - Kiuwan LifeCycle
This module is included with continuous licenses. It helps you create audits of your analysis results and how they change over time. This module is added to Kiuwan Code Security if you buy a continuous subscription.
It covers the following standards:
- SANS 25
- CERT-Java/C/C++
- WASC
- PCI-DSS
- NIST
- MISRA
- BIZEC.
...and the list is continuously growing!
Learn more about how Kiuwan Code Security performs on the OWASP Benchmark here.
The chart below shows the performance of Kiuwan Code Security for the latest version of the OWASP Benchmark, as of November 2019. The results show that Kiuwan (at position K) detected 100% of true positives, correctly identifying all vulnerabilities present in the test application.
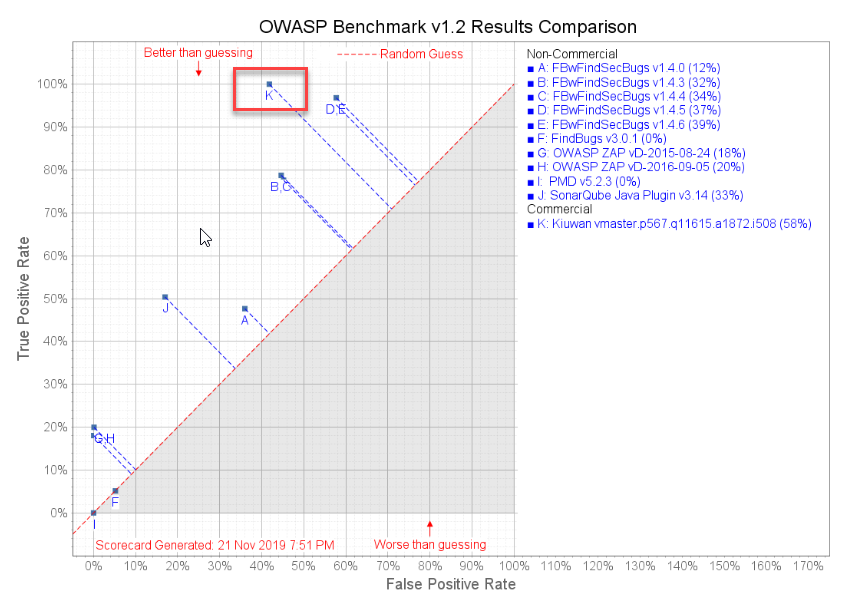
For more details about the OWASP Benchmark and Kiuwan Code Security, read our original blog post from 2017, or review our most recent results and run your own test.
Kiuwan is currently a modest income company, and our revenue does not meet the target for inclusion in the current Gartner Magic Quadrant. However, we are growing rapidly and anticipate that this will change in the near future.
Kiuwan solutions are trusted by 500+ companies worldwide, including:
To learn more, read verified reviews from Kiuwan users at the following third-party sites:
There are two options:
- Build an Action Plan based on the criteria that are more important to you (available man-power, high-security vulnerabilities...)
- Ask Kiuwan Code Security to build an Action Plan for you based on your preferred strategy (e.g. I want to reach a 5-star rating)
- Analyzing in the cloud: In this case, you upload the source code to the Kiuwan Cloud. The source code is then deleted as soon as the analysis is finished.
- Analyzing locally: In this case, analyzing locally, the source code never leaves the local machine: it is locally analyzed. The generated results are encrypted and securely uploaded to Kiuwan Cloud. Once received, those results are used to calculate metrics to be displayed to the Kiuwan users.
Your results (defects, metrics, etc.) are uploaded securely to the Kiuwan Cloud, and you will view them in the dashboard.
Secure Socket Layer (SSL) technology protects information sent to Kiuwan using encryption and authentication server. It ensures that your data in transit is safe, secure, and visible only to registered users in your organization.
We tested the speed to give you an idea and these are the results:
- 577k LoC in Java ~ 15 minutes
- 32k LoC in Python in ~ 12 minutes
- 9m LoC in C/C++ (Juliet v1.3) in ~ 23 hours
Results may vary.
- Software characteristics
- Security, efficiency, maintainability, reliability, and portability
- Global Indicator
- The weighted average of the above software characteristics through a complex algorithm. This considers the severity of the defects, the weight of the category in which the defect is, the analyzed code volume, and the criticality of the language for Kiuwan users. This algorithm can be customized.
- Effort to Target
- The amount of work effort needed to reach a defined goal.
- Risk Index
- A representation of the potential problems that could arise by not paying attention to the security and quality of your source code. Any value greater than 0 should be observed and actions should be done to decrease the number.
- Click the Management menu on the dashboard;
- Select Download Kiuwan Local Analyzer.
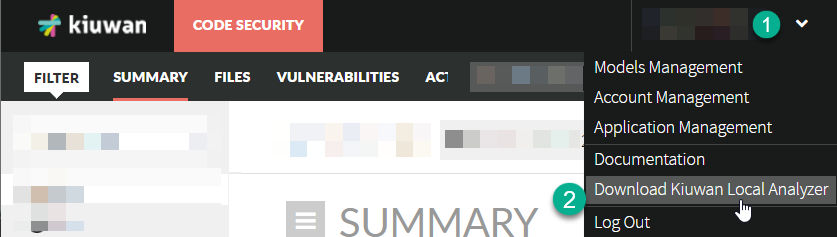
If you want to use the Kiuwan Local Analyzer you also need Java Runtime Environment installed on your computer. Read more about the requirements here: Installation Requirements for Kiuwan Local Analyzer
Language | Extensions |
|---|---|
ABAP | abap,bsp |
ActionScript | as |
ASP.NET | asax,ascx,ashx,asmx,aspx,master |
C | c,h,pc |
COBOL | cob,cbl,cpy,pco |
C++ | h,hh,cpp,hpp,cc,pc |
C# | cs,cshtml |
| Go | go |
HTML | htm,html,xhtml |
Informix | sql,4gl |
Java | java |
JavaScript /TypeScript | js,xsjs,ts,tsx |
JCL | jcl,prc |
JSP | jsp,jspx,xhtml |
| Kotlin | kt,ktm,kts |
Natural | nls,nlp,nlh,nlm,nss,nsp,nsh |
Objective C | h,m |
OracleForms | oforms |
PHP | php,php3,php4,php5,php6, phps,phtml |
PL-SQL | sql,sf,sps,spb,sp,fnc,spp,plsql,trg,st,prc,pks,pkb,pck |
PowerScript | sru,sra,srw,srf,srs,srm,srx |
Python | python,py |
RPG4 | rpg,rpg3,rpg4,rpgle,dspf,mbr |
| Scala | scala |
| Swift | swift |
Transact-SQL | sql,tsql,sp |
VisualBasic 6 | bas,frm,cls |
VB.NET | vb |
Find more details here: https://www.kiuwan.com/languages/
The list keeps on growing! Contact our support team to find out which languages will be added in the future.
Please visit Export an Action Plan for further information.
Please visit Developers - Integrations for a full list of possibilities.
The Kiuwan Applications also have a REST API that can be used for more advanced integrations and interactions.
Question not answered?
We can help!
I'm not a client (yet)
Our sales team will be happy to help you.
- No labels