
Welcome to the final article in our blog series on the OWASP Top 10 Security Vulnerabilities. In this article, we’ll take a detailed look at OWASP Top 10 2017 A10 – Insufficient Logging & Monitoring.
Insufficient logging and monitoring of computer systems, applications and networks provide multiple gateways to probes and breaches that can be difficult or impossible to identify and resolve without a viable audit trail.
Typical log architecture generates both security and operational logs, analyzes, stores and monitors those logs. This is not only important for dealing with the threats resulting from insufficient logging and monitoring but for regulatory compliance as well. With today’s varying levels of application, server and network communication, it’s imperative to maintain more than a modicum of best practices pertinent to your industry and to your organization. Vulnerabilities and breaches often take the better part of a year to find — up to 200 days in some cases — and can cost enterprises millions of dollars.
Security logs are different than operational logs. Operational logs (aka operating system logs) will include routine system events like logins and shutdowns on workstations, servers, and networks. They will also derive logs from associated security software. Security logs from security software include logs from firewalls, routers, and host or network security devices and services.
Operational logs are indispensable for honing in on questionable activity that may lead to an attack on your most sensitive and mission-critical data. However, security logs are often deemed supplementary, depending on what a particular company requires for an investigation into a vulnerability or threat. Either way, both types of logs are invaluable for identifying and resolving insufficient logging and monitoring vulnerabilities.
Basic vulnerabilities include:
Penetration testers and auditors should test and validate computer systems, applications, related servers, and networks periodically. Deficiencies are vulnerabilities that need to be addressed as soon as they are identified.
You do not want to stop logging if you find yourself vulnerable. While insufficient logging and monitoring vulnerabilities create a high prevalence of breach potential, abruptly stopping the logging may alert savvy attackers to the fact that your sensitive and mission-critical data may be exposed and easily exploited. Adhere to your company’s best practices if your company has established them.
Prevention is key. Not all logs are clear or readable. They should be monitored and validated at a pace commensurate with your business impact.
If you do not mandate that your company collect, store, maintain and monitor logging activity, then you are opening yourself to costly security breaches that you cannot easily track. Audit trails provide your IT staff with the tools for the identification, prioritization, investigation, and resolution of exploitation.
Most U.S. states and territories have enacted security breach notification laws. Therefore, it is in the best interests of all private and government entities to comply with all national and state regulations. Center to compliance is logging and monitoring all events that involve your company. Here are a few regulations that you may be required to comply with:
The Control Objectives for Information and Related Technology (COBIT) has more information to guide you regarding best practices and increasing regulatory demands.
You can further minimize insufficient logging and monitoring exploitation by establishing feasible policies and procedures that mandate consistency and compliance throughout your company’s infrastructure.
Doing so will:
Whether your organizational structure needs to facilitate a single management system for a small business or is based on several types of enterprise structures that demand interoperability for regulatory compliance, it is imperative to train those involved, including developers, and re-train often as new regulations emerge or security breaches mandate change. Something as seemingly innocuous as realigning work stations with a new server merits retraining personnel.
You don’t want to engage in damage control. The levels of log management can be overwhelming to sift through. There are many passive commercial and open-source log management frameworks available that can automate the monitoring process. Penetration testers and auditors tend to be resource-intensive and expensive, but sometimes necessary.
There has to be a new mindset. Simply keeping attackers out of company business is passe and dangerous–whether you are a small business or a major corporation. It’s not enough to find the who and eradicate the threat. Today you have to know why your company is vulnerable and how to prevent probing eyes and attacks before they start. Not only will it keep your company viable, but also compliant with ever-changing regulations that mandate an audit trail.
You can’t resolve a breach if you don’t detect it. By defining (and verifying) the roles and responsibilities of those involved in log management at both the systemic and operational levels, companies can mitigate breaches and have ready audit trails to resolve breaches.
About OWASP Top 10 2017 – A10 Insufficient Logging & Monitoring
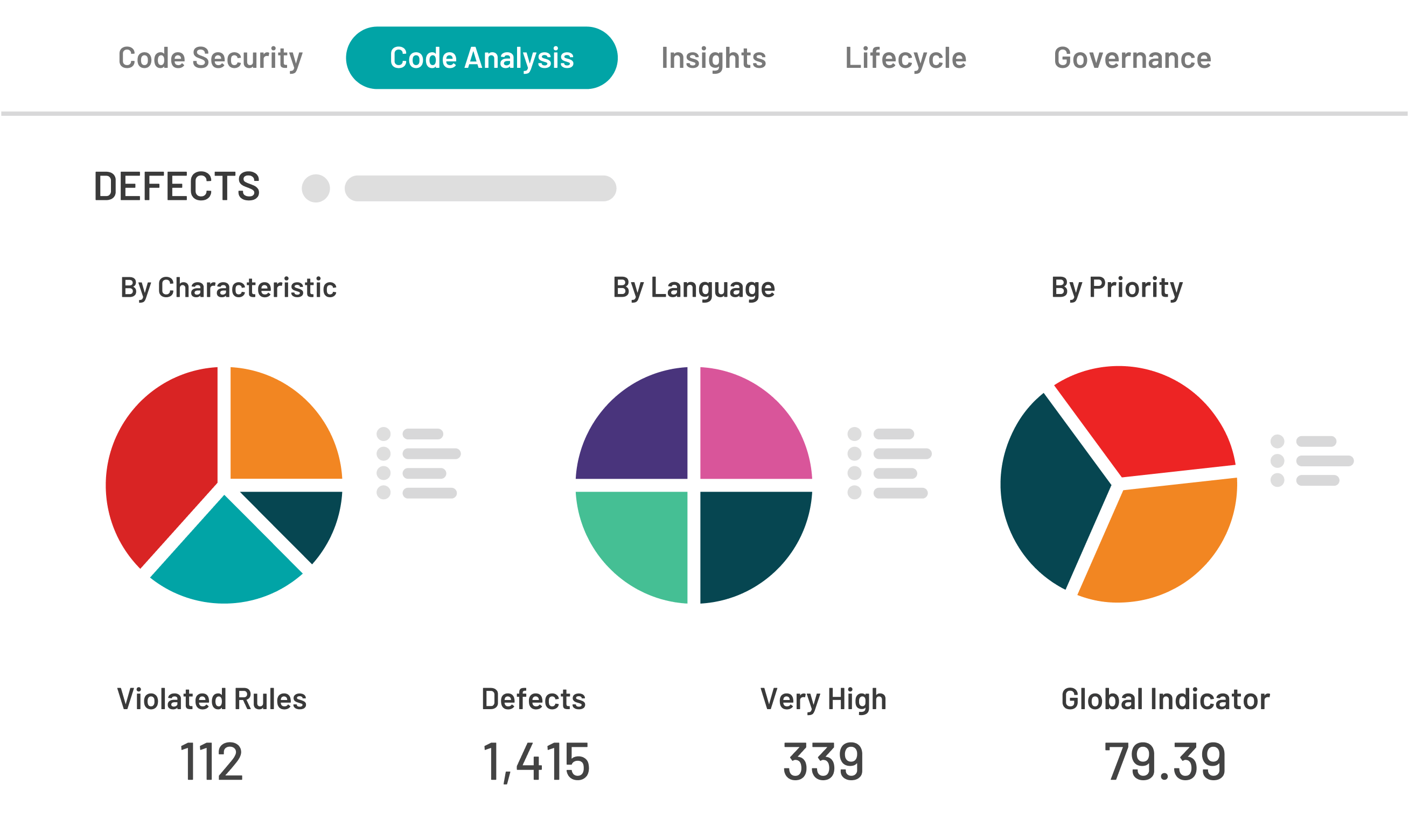
Kiuwan Code Security can help you identify and remove security vulnerabilities from your code.


