Software Composition Analysis (SCA) is a process that identifies and manages open-source components within a codebase. It is essential for ensuring that applications are secure, compliant, and up-to-date.
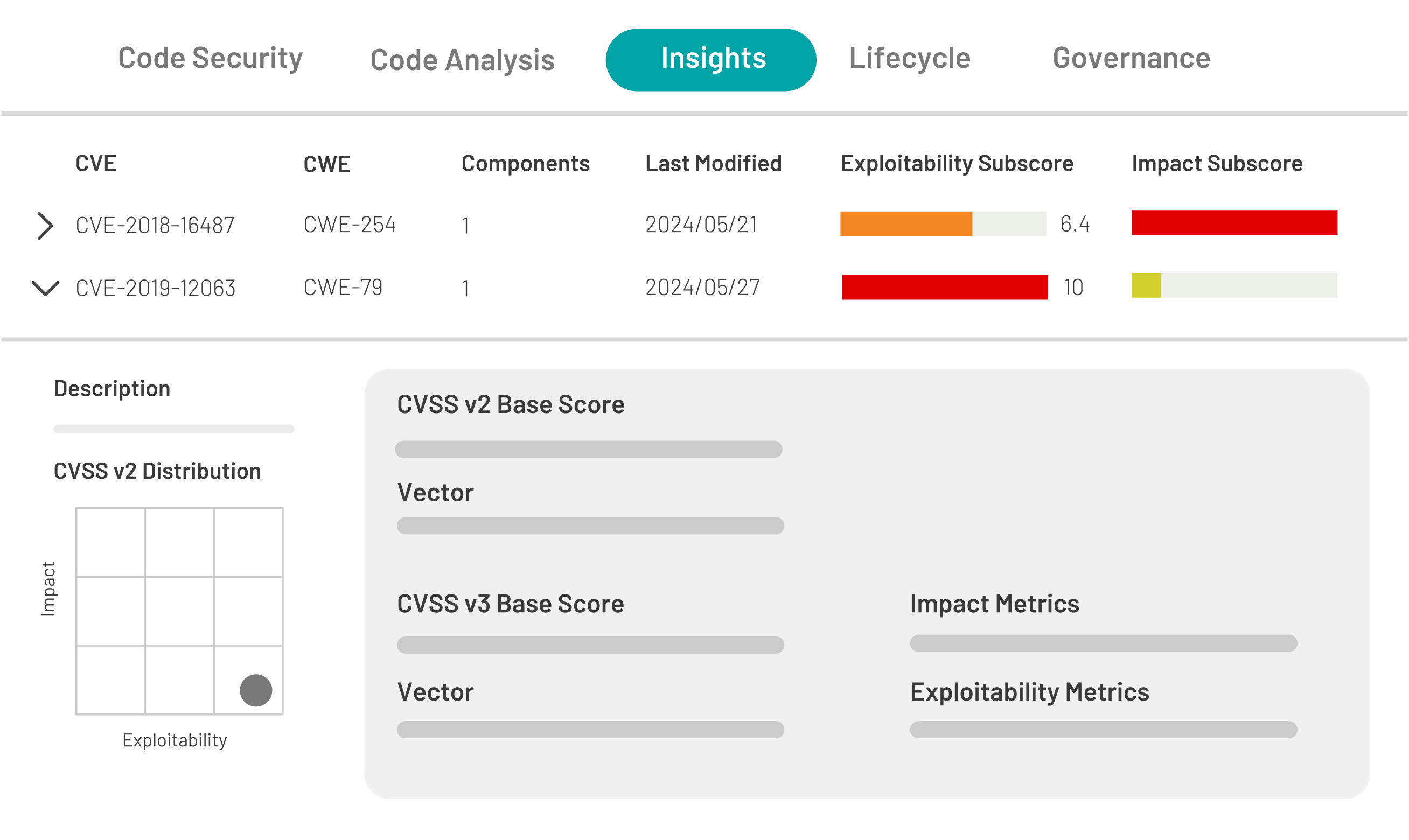
SCA helps developers and organizations detect vulnerabilities, license compliance issues, and outdated components. Tools like Kiuwan Insights, automate this process, offering continuous monitoring and actionable insights that help mitigate risks and enhance overall software quality. By proactively managing open-source dependencies, SCA empowers teams to build safer and more reliable applications.