

Data is no longer merely a tool used to improve business strategy. Increasingly, data is an asset that drives the growth of organizations, especially in businesses that handle large amounts of personally identifiable information (PII) such as banks and financing companies. Malicious actors target this data because of its value in committing identity theft, defrauding credit card companies, and stealing directly from bank accounts.
Data breaches occur frequently and come with a high price tag. The shift to a digital-first economy that was hastened by the pandemic has increased the average cost of a data breach, which, according to IBM Security’s Cost of a Data Breach Report 2021, went up 10% from 2020 to 2021. The average total cost of a data breach is $4.24 million, which includes the cost of restoring data and services after a breach as well as the cost of lost business.
There’s a striking difference, however, in the average cost for businesses that fully implemented security AI and automation and those that didn’t. The costs for a data breach in organizations that failed to deploy AI and automated security measures were 80% higher than the costs for those that did. These numbers highlight the fact that data security is vital for all businesses, especially those that deal with PII.
Data States and Security Vulnerabilities
Protecting data in all of its states is fundamental to effective data security. Data can change states frequently or remain in one state for its entire lifecycle. There are different surfaces of attack in each state when data is vulnerable to attack, clandestine capture, and corruption. A fully-formed data security plan needs to include automated protocols to protect data confidentiality and integrity while it’s in use, in motion, and at rest.
Data at rest
Data that isn’t currently being accessed or transferred is termed “at rest.” Data at rest is stored on a hard drive, a storage area network (SAN), or on off-site backup servers. Because the data has reached its destination, it’s considered stable compared to other data states. Methods for protecting data at rest include encryption, hierarchal password protection, secure servers, and outside data protection services.
Whatever encryption method is used should be capable of AES-256 encryption. Some cyberattacks rely on brute force or stealth and can remain undetected for long periods of time. Even attacks that rely on exfiltrating data at thresholds below the alert level can’t crack AES-256 encryption, at least not currently. However, cybercriminals are nothing if not inventive, so data security has to be baked into the entire development process at every step along the way.
Data in motion
When data is being transferred between locations or within computer systems, it’s vulnerable to attack. Data in motion — which also includes data stored in a computer’s RAM that’s ready to be accessed or data moving between cloud storage and local storage — can be protected by encrypting the data before transfer or by encrypting the passage tunnel. Again, the encryption should use AES-256 encryption for the best protection.
Data in use
The most vulnerable data state is data in use. It’s directly accessible to one or more users, so encryption at this point is essential.
Additional methods of data protection for data in use include:
-Implementing a zero trust model including authentication of all users at all phases of access
-Strong identity management protocols
-Well-maintained permission profiles
-Financial Industry Data Protection Regulations

In the U.S., the Federal Trade Commission has broad powers of enforcement to protect consumers against unfair or deceptive practices and to enforce federal privacy and data protection regulations. However, there isn’t one overarching data protection legislation. Rather, there are hundreds of various state and federal laws that apply to different industries or situations that are designed to protect PII.
The shift to a digital-first business landscape and the rise in remote working have increased data security challenges. Because of this, regulatory compliance in banking and finance security has become even more vital in recent years.
A few of the most relevant data protection regulations that apply to the financial services and banking industries include:
The Gramm-Leach-Bliley Act (GLBA)
Also called the Financial Services Modernization Act, this legislation was introduced in 1999. Compliance with GLBA is mandatory for financial institutions and requires the following:
-Financial privacy statement issued to consumers that explains what information is collected, how it’s used, and where it’s shared
-A security plan that describes how the institution will protect the client’s nonpublic information
-Safeguards against outside actors manipulating clients into giving up their personal information
The Sarbanes-Oxley Act (SOX)
Passed in 2002, SOX was designed to protect investors from fraudulent reporting after several cases of widespread fraud, including the Enron scandal. SOX compliance involves establishing internal controls to prevent fraud and abuse, protect data privacy, and hold senior managers accountable for the accuracy of financial reporting.
New York Department of Financial Services regulation (NYDFS)
The NYDFS was introduced in 2017 to address the growing threat of cybercrime to financial institutions. It applies to all organizations regulated by the Department of Financial Services and their out-of-state and overseas branches. It requires firms to assess their cybersecurity risk and implement a comprehensive plan to mitigate their risks.
Software Security
The complexity of data protection and the broad surface of attack given the myriad of points of access calls for software security to be an integral part of all phases of the software supply chain. The widespread adoption of cloud computing, remote access, and open-source code has rendered the perimeter model of software security obsolete.
Instead, organizations need to approach security from a DevSecOps perspective, where security is a primary consideration at every location along the continuous integration and continuous deployment (CI/CD) pipeline. Testing code for security flaws early in the process allows for quicker detection and remediation.

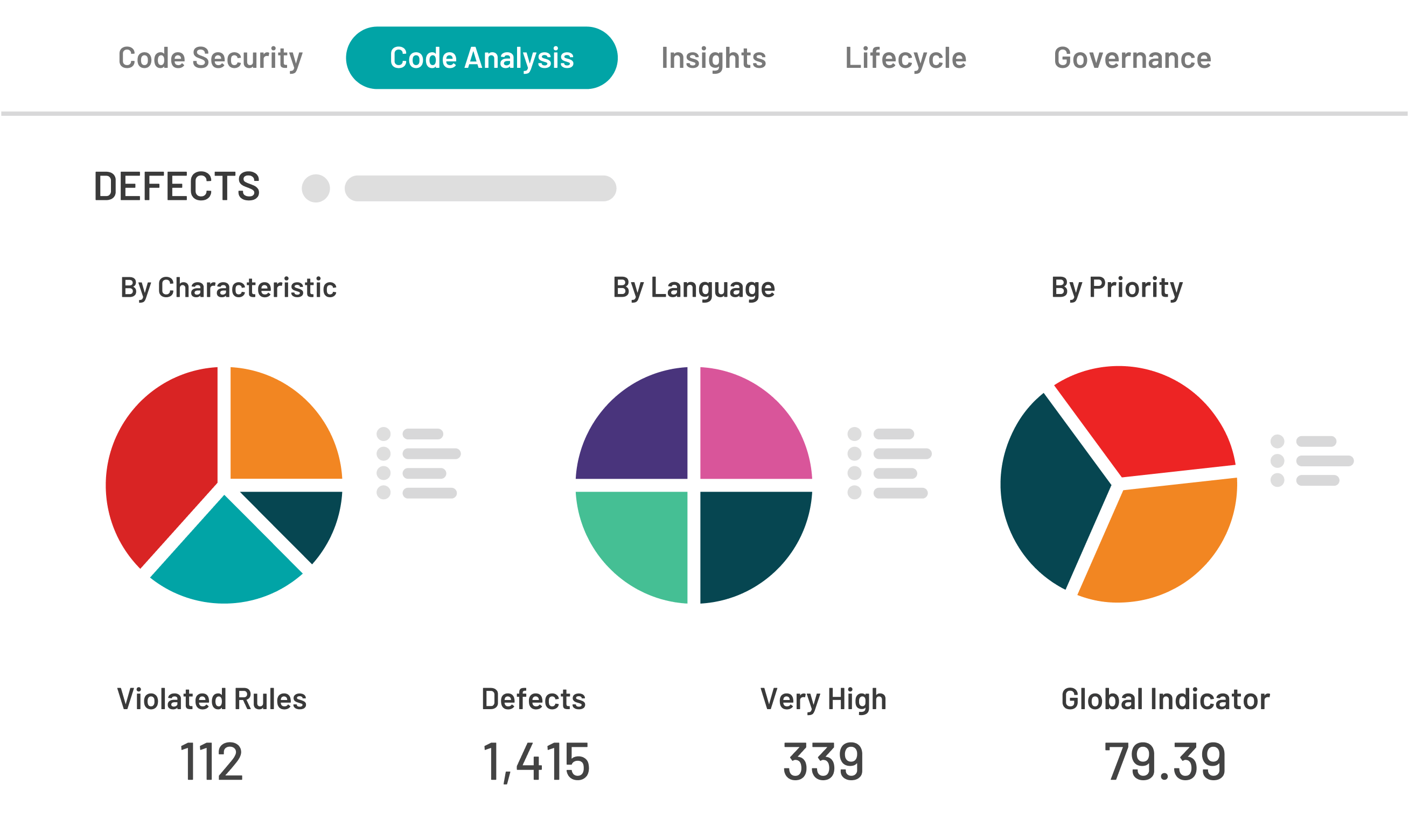
There are two primary methods for testing code early in the CI/CD pipeline that examine uncompiled code for security vulnerabilities. Software composition analysis (SCA) and static application security testing (SAST) can eliminate many code flaws that result in deploying applications that are vulnerable to cyberattacks such as injection, leaks, overflows, and cross-site scripting. Early detection and remediation help alleviate an array of security vulnerabilities including: -Broken access control -Buffer overflow -Cryptographic failures -Execution with unnecessary privileges -Injection -Missing authentication -Missing encryption -Vulnerable and outdated components -Path traversal SCA Kiuwan’s Insights Open Source (SCA) testing scans code for occurrences of open source software (OSS) which might include vulnerabilities. Open-source code is widely used because it’s efficient and allows developers to deploy applications quickly. However, unpatched security vulnerabilities in open-source code are a significant source of risk. Additionally, without a clear understanding of the often-conflicting licensing terms of various open-source software programs, organizations can put their intellectual property rights at risk. SCA testing can resolve any licensing issues when using code snippets from OSS applications. SAST Code Security (SAST) combined with SCA allows developers to test and fix code earlier in the process when it can be done with less effort and expense. SAST scans for vulnerabilities before the code is executed to prevent it from deploying and becoming an exploitable weakness. SAST is compatible with all major languages and compliant with all of the most stringent security standards in the financial industry. SAST integrates with leading DevOps tools across the software development lifecycle, so it’s easy to incorporate security into the DevOps process early on. Automated code scanning allows developers to create an action plan to reduce their security risks. Kiuwan lets teams shift left and bake security into application design.


