Kiuwan provides out-of-the-box "rules" based on industry security standards, such as CWE/SANS 25, OWASP Top 10Code Security is an OWASP corporate member and CWE certified. It is also compliant with SANS 25, CERT-Java/C/C++, WASC, PCI-DSS, NIST, MISRA, and BIZEC.
Visit our blog post on Security Standards in Software Development to learn more.
What is the CWE Common Weakness Enumeration?
The Common Weakness Enumeration (CWE) is an extension of the Common Vulnerabilities and Exposures (CVE) list compiled by MITRE, a federally-funded, non-profit organization that manages research and development centers supporting government agencies like Homeland Security.
...
OWASP is an international non-profit organization dedicated to analyzing, documenting and spreading the principles for the safe and vulnerability-free software development.
They produce a document called OWASP Top 10. As they say: “The OWASP Top Ten is a powerful awareness document for web application security. The OWASP Top Ten represents a broad consensus about what the most critical web application security flaws are. Adopting the OWASP Top Ten is perhaps the most effective first step towards changing the software development culture within your organization into one that produces secure code“.
You can visit our Kiuwan Blog and learn how Kiuwan can help you on assessing and fixing your security vulnerabilities according to OWAS Top Ten:
- OWASP Top 10: how to discover vulnerabilities in your Java applications
- OWASP Top 10: how to discover vulnerabilities in your C# applications
What is the OWASP Top 10 for 2017?
For 2017, the OWASP Top 10 Most Critical Web Application Security Risks are:
- A1 Injection ( https://www.kiuwan.com/blog/owasp-top-10-a1-injection )
- A2 Broken Authentication and Session Management (https://www.kiuwan.com/blog/owasp-top-10-2017-a2)
- A3 Sensitive Sata Exposure (https://www.kiuwan.com/blog/owasp-top-10-2017-a3-sensitive-data-exposure-identify-your-weaknesses/)
- A4 XML External Entities (XXE) (https://www.kiuwan.com/blog/a4-xml-external-entities-xxe/)
- A5 Broken Access Control (https://www.kiuwan.com/blog/owasp-top-10-2017-a5-broken-access-control/)
- A6 Security Misconfiguration (https://www.kiuwan.com/blog/owasp-top-10-2017-a6-security-misconfiguration/)
- A7 Cross-Site Scripting (XSS) (https://www.kiuwan.com/blog/owasp-top-10-2017-a7-cross-site-scripting-xss/)
- A8 Insecure Deserialization (https://www.kiuwan.com/blog/owasp-top-10-2017-a8-insecure-deserialization/)
- A9 Using Components with Known Vulnerabilities (https://www.kiuwan.com/blog/owasp-top-10-2017-a9-using-components-with-known-vulnerabilities/)
- A10 Insufficient Logging and Monitoring (https://www.kiuwan.com/blog/owasp-top-10-2017-a10-insufficient-logging-monitoring/)
You can browse Kiuwan rules by OWAS Top10 to find what Kiuwan rules complies with what OWASP security risks.
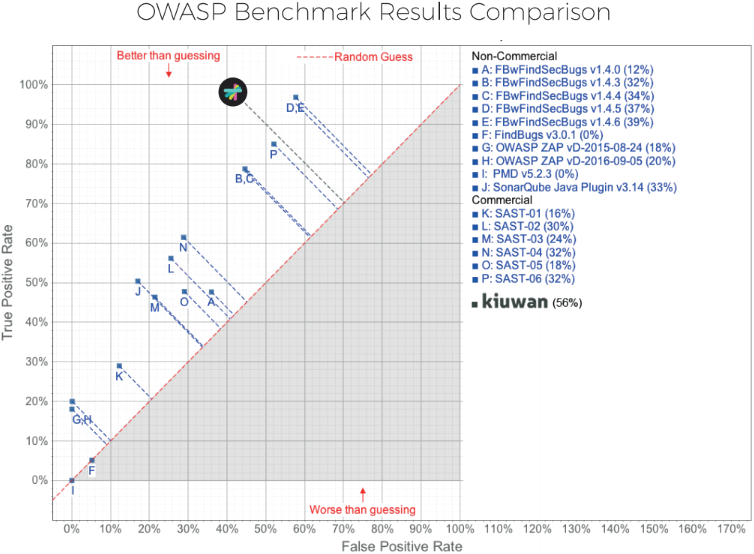
How does Kiuwan perform in the OWASP Benchmark?
The OWASP Benchmark is a test suite designed to evaluate the coverage and accuracy of automated vulnerability detection tools.
We have run Kiuwan against the OWASP Benchmark test cases and here you have the results (compared to open and commercial tools).
Kiuwan is right up there detecting almost 100% of true positives !!
The Benchmark contains thousands of test cases that are fully runnable and exploitable.
It considers 11 different types of vulnerabilities, including several injection types such as XSS, weak encryption or trust boundary. For every type, the test cases have real vulnerabilities (true positives) and fake vulnerabilities (false positives) to challenge the tools.
...
Learn more about how Kiuwan Code Security performs on the OWASP Benchmark here.
Please, read https://www.kiuwan.com/blog/owasp-benchmark-kiuwan/
Do you want to build and run by yourself the OWASP Benchmark with Kiuwan?
Then, have a look at https://www.kiuwan.com/blog/owasp-benchmark-diy/
How does Kiuwan help with security in Cobol, RPG and ABAP?
Kuwan Code Security includes detection rules that cover so-called "legacy" languages.
Please visit below links for further info:
...