OAuth 2.0 is an authorization framework that allows software applications to access protected resources that belong to somebody or something. The software applications can obtain total or partial access to the protected resources, either on behalf of a resource owner by orchestrating an approval interaction between the resource owner and the HTTP service or by allowing the software applications to obtain access on their own behalf.
Additionally, OIDC adds a simple identity layer (adding end-users authentication-related data in the payload) on top of the OAuth 2.0, making simple integration with external systems that support some of the grant types defined in OAuth 2.0 specification (OAuth 2.0 Authorization Framework) i.e. most major online services nowadays.
Contents:
When configured, a Kiuwan user can authenticate against an OAuth/OIDC server, and access Kiuwan resources.
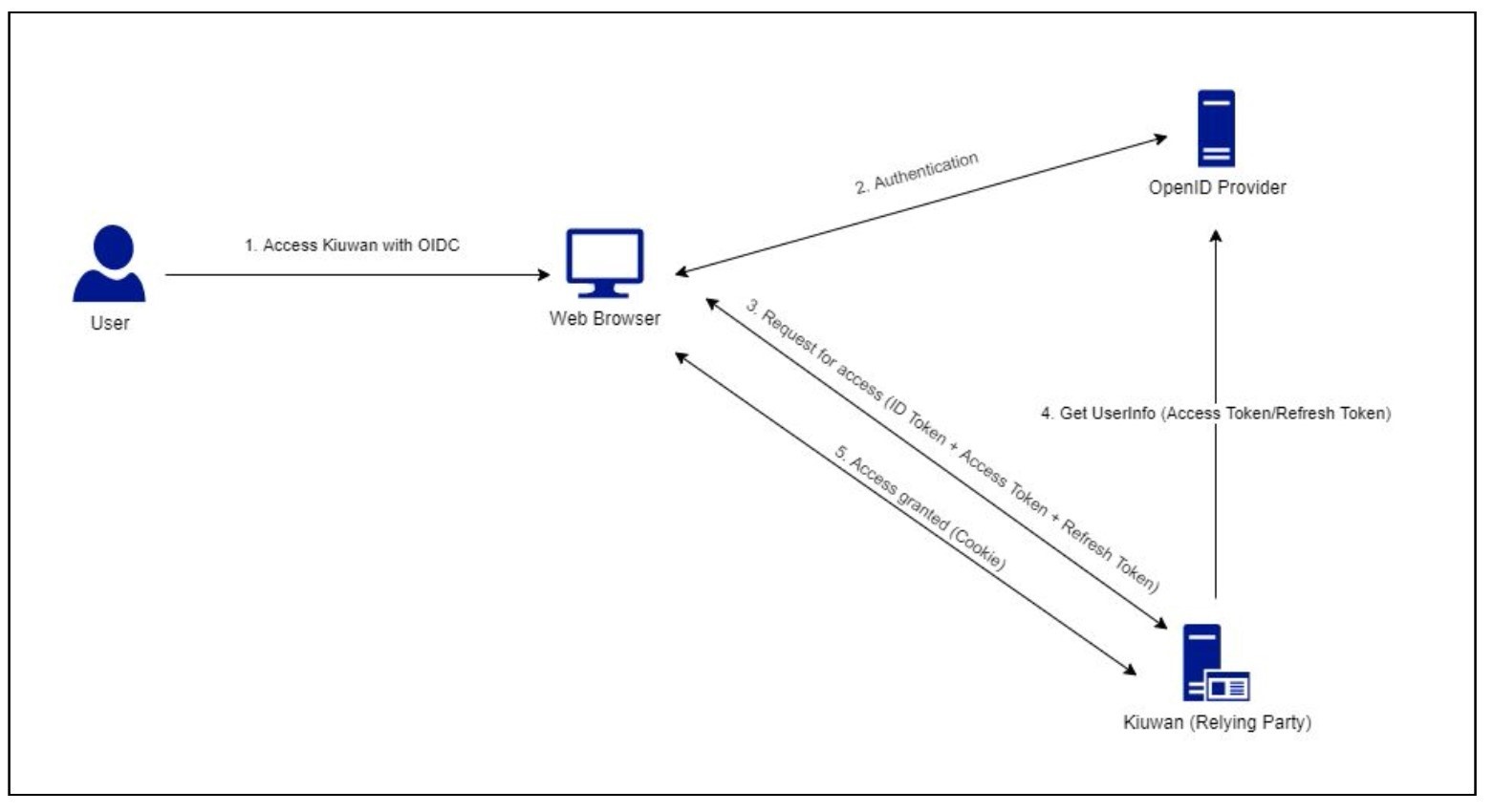
Before the user can start using Web Browser SSO flow, the administrator of the OpenID Provider in their organization must first have registered Kiuwan as a Relying Party, and subsequently, the account owner of the Kiuwan user account must have registered their OpenID Provider in Kiuwan.
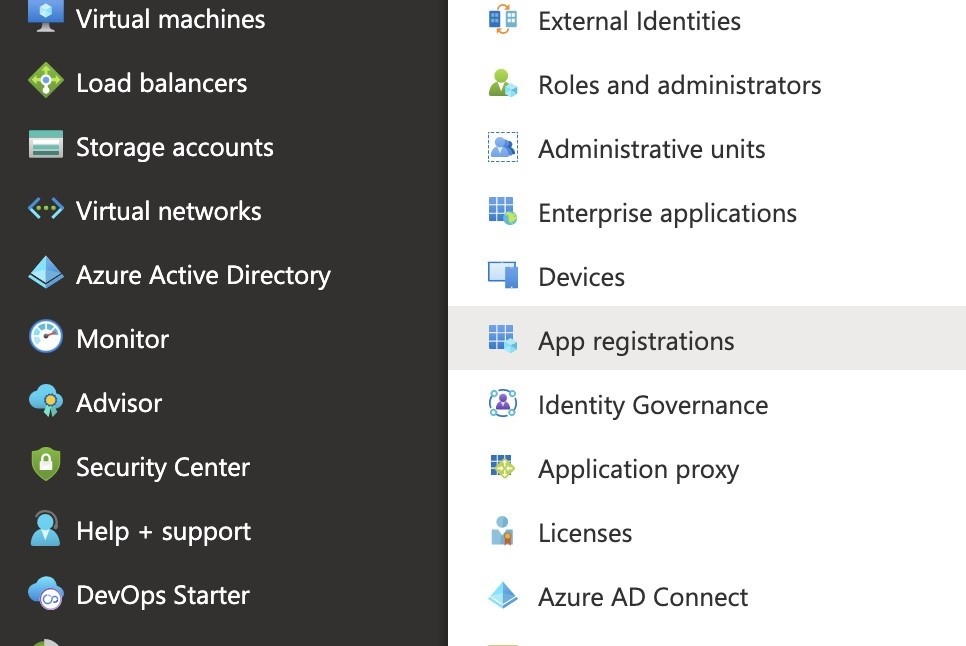
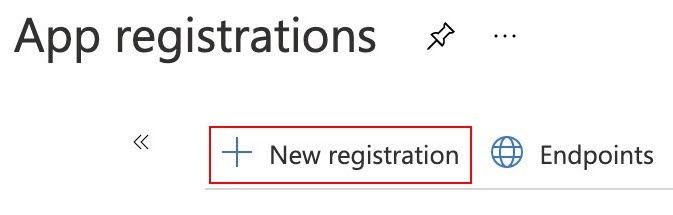
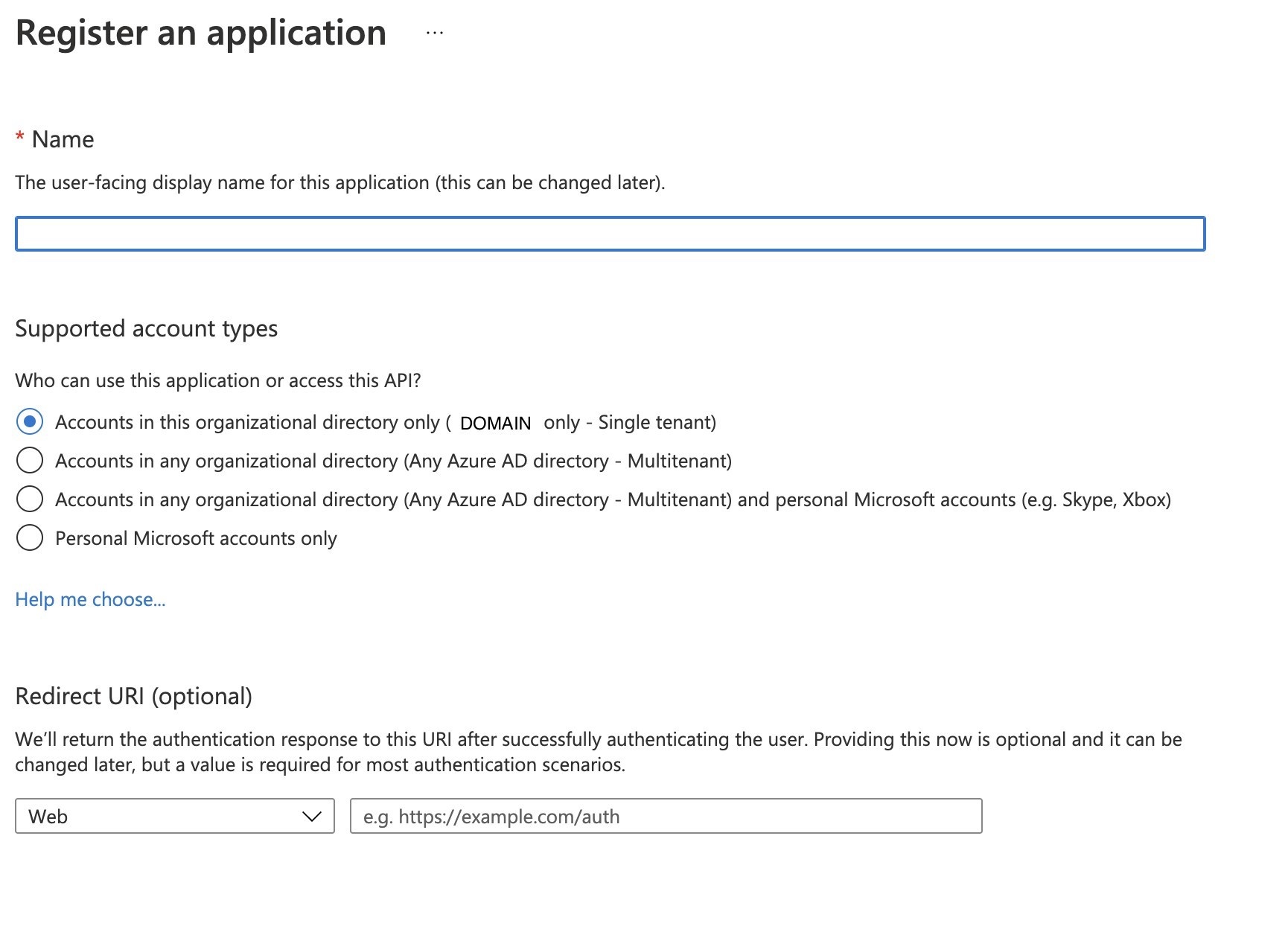
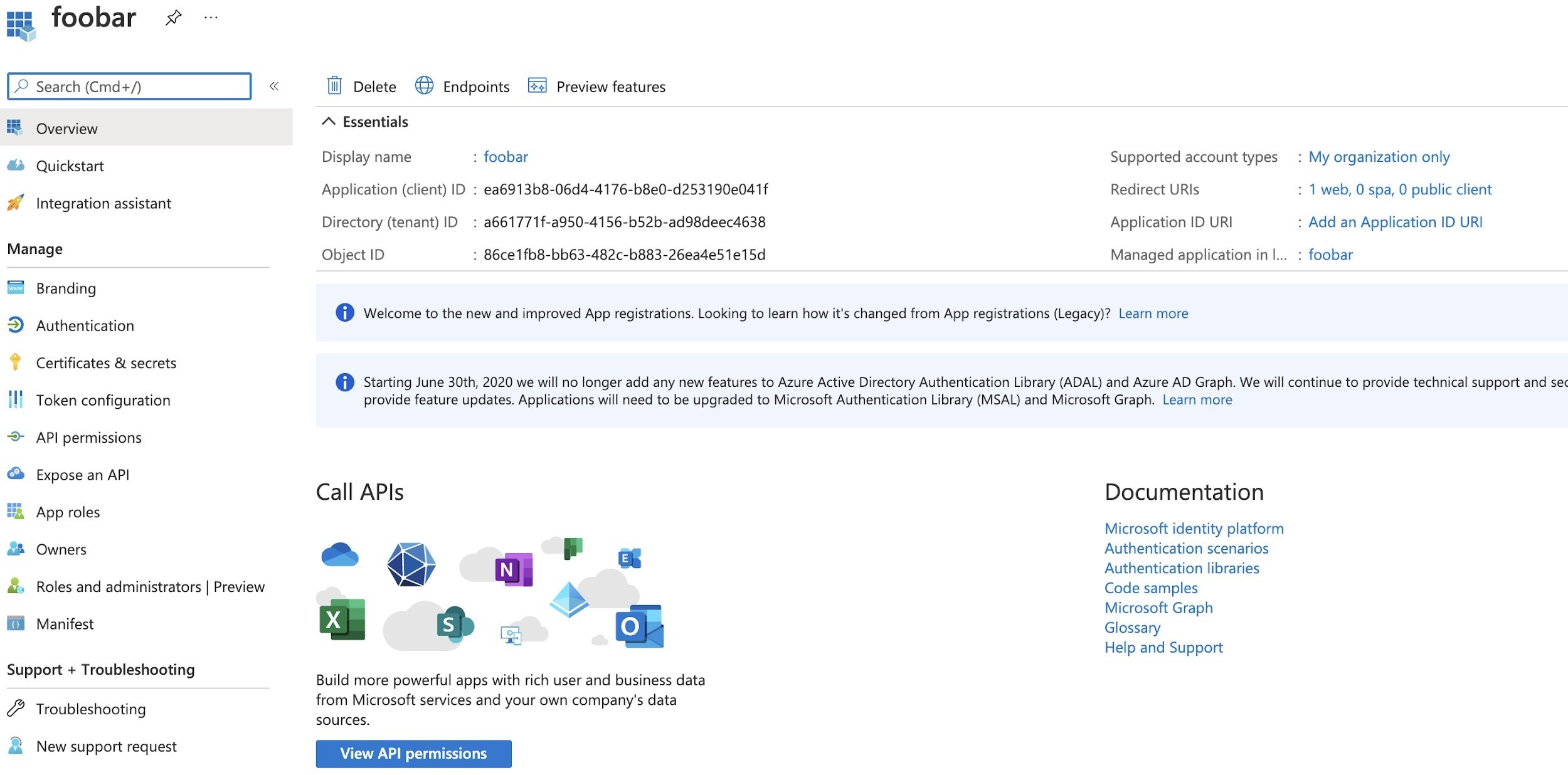
The following describes how to setup Kiuwan as a registered application on Azure ADFS, any other OAuth2.0/Open ID Provider with a similar configuration.
To enable the authentication through an OAuth/OIDC server when configuring Kiuwan as a client application is required to be obtained from OAuth Issuer the following:
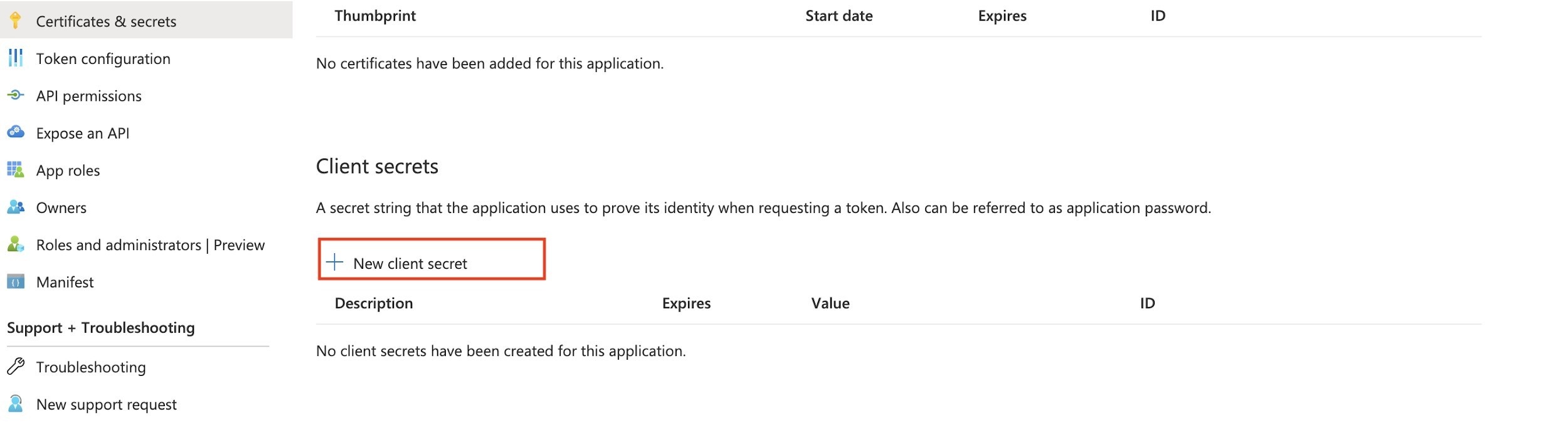
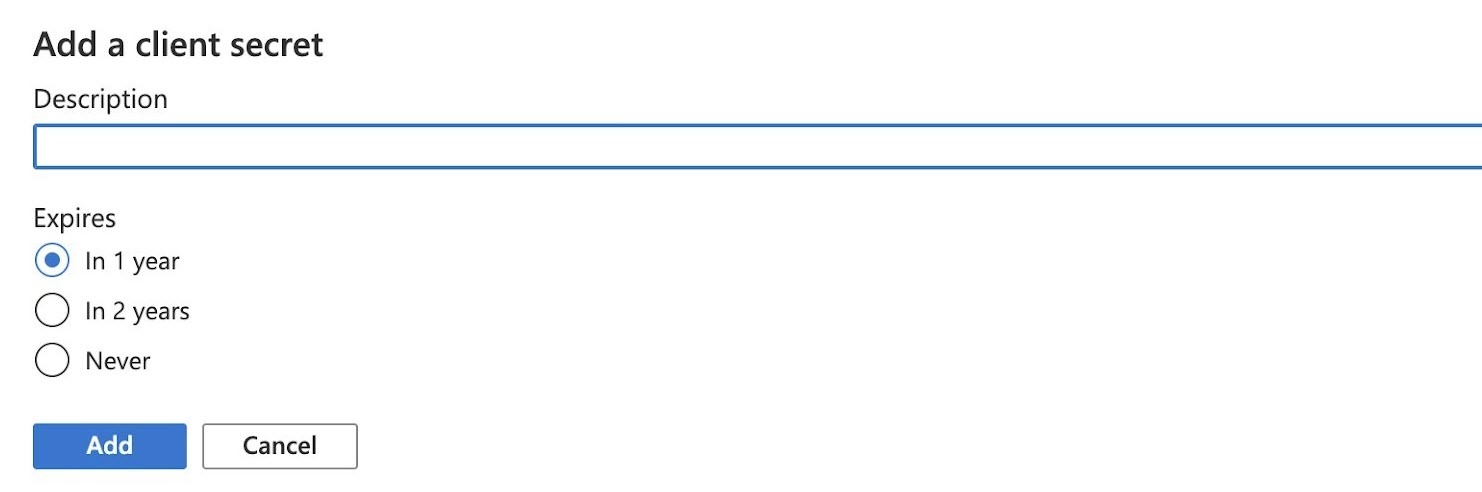
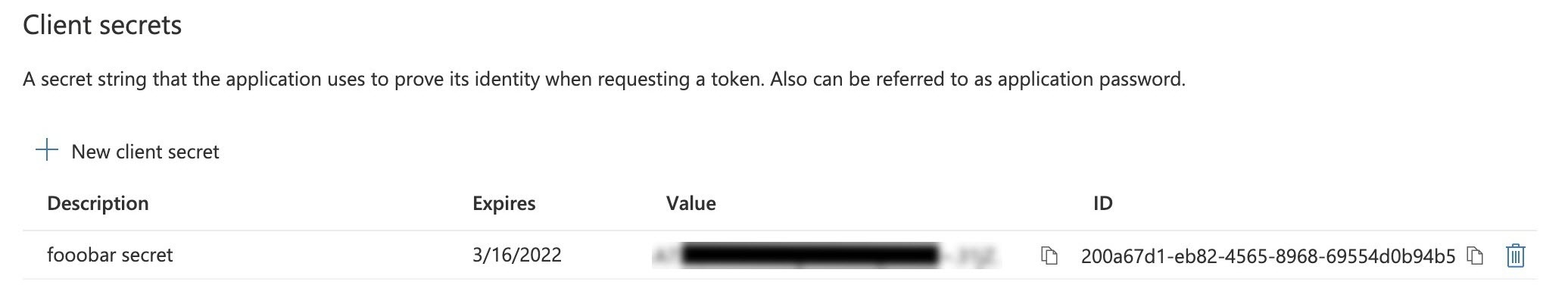
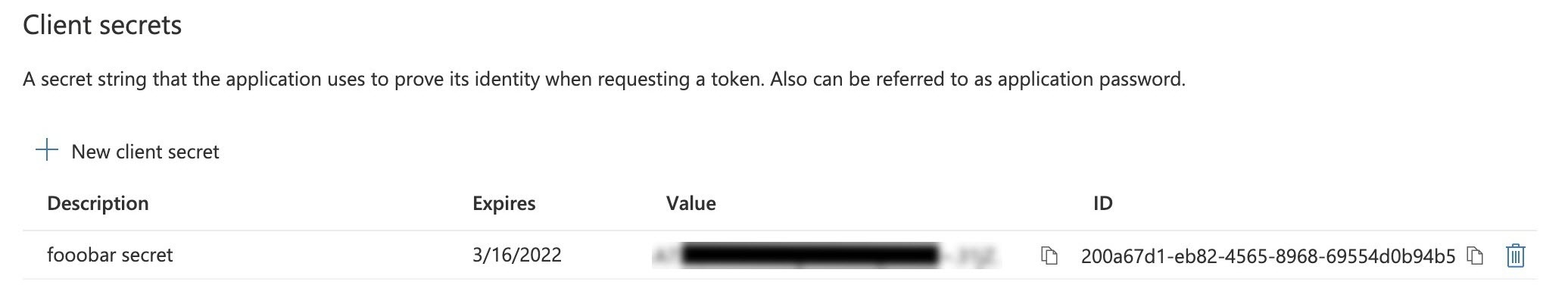
Copy this value to a temporary location as it will be needed later and after the screen is closed the access to the secret value is lost. Ideally, paste it directly into the OAuth/OIDC configuration at Kiuwan described in the next chapter.
In the previous steps, you have created a new registry for Kiuwan to integrate with OAuth/OIDC server.
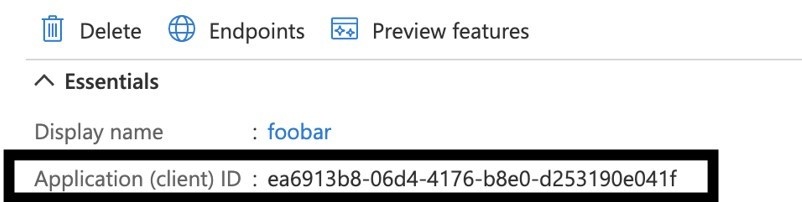
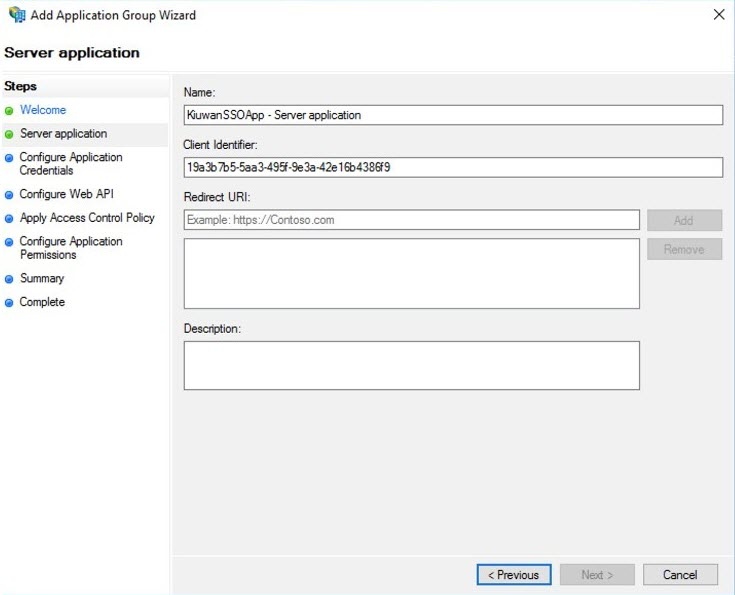
The following information was generated, that would be needed in configuring Kiuwan to use this registry:
Application ID:
Application Secret:
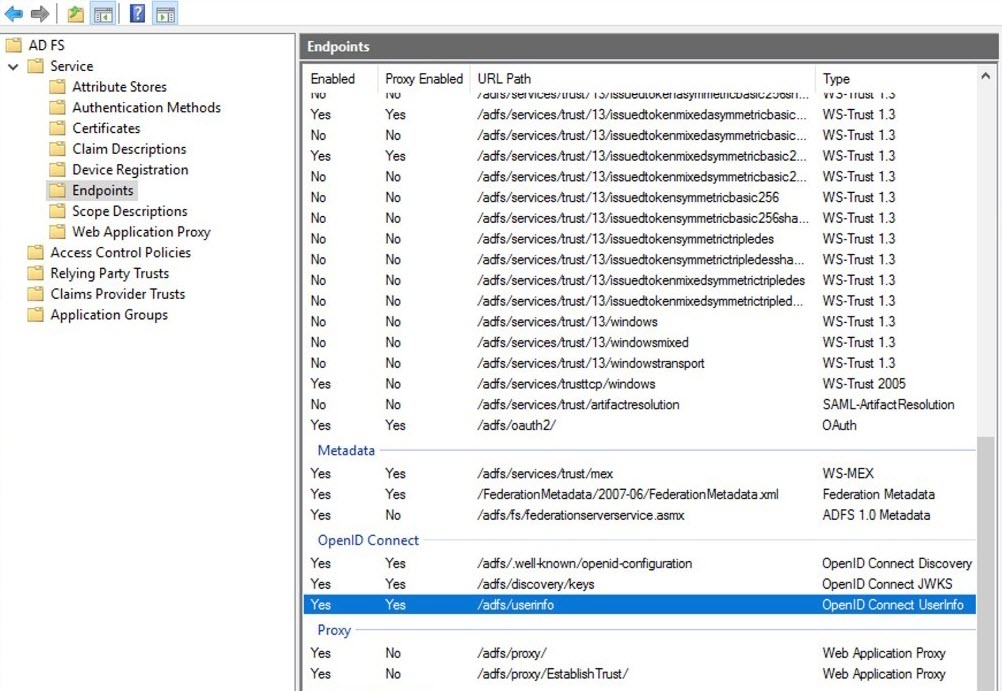
Additionally, you would also need to collect the following endpoints:


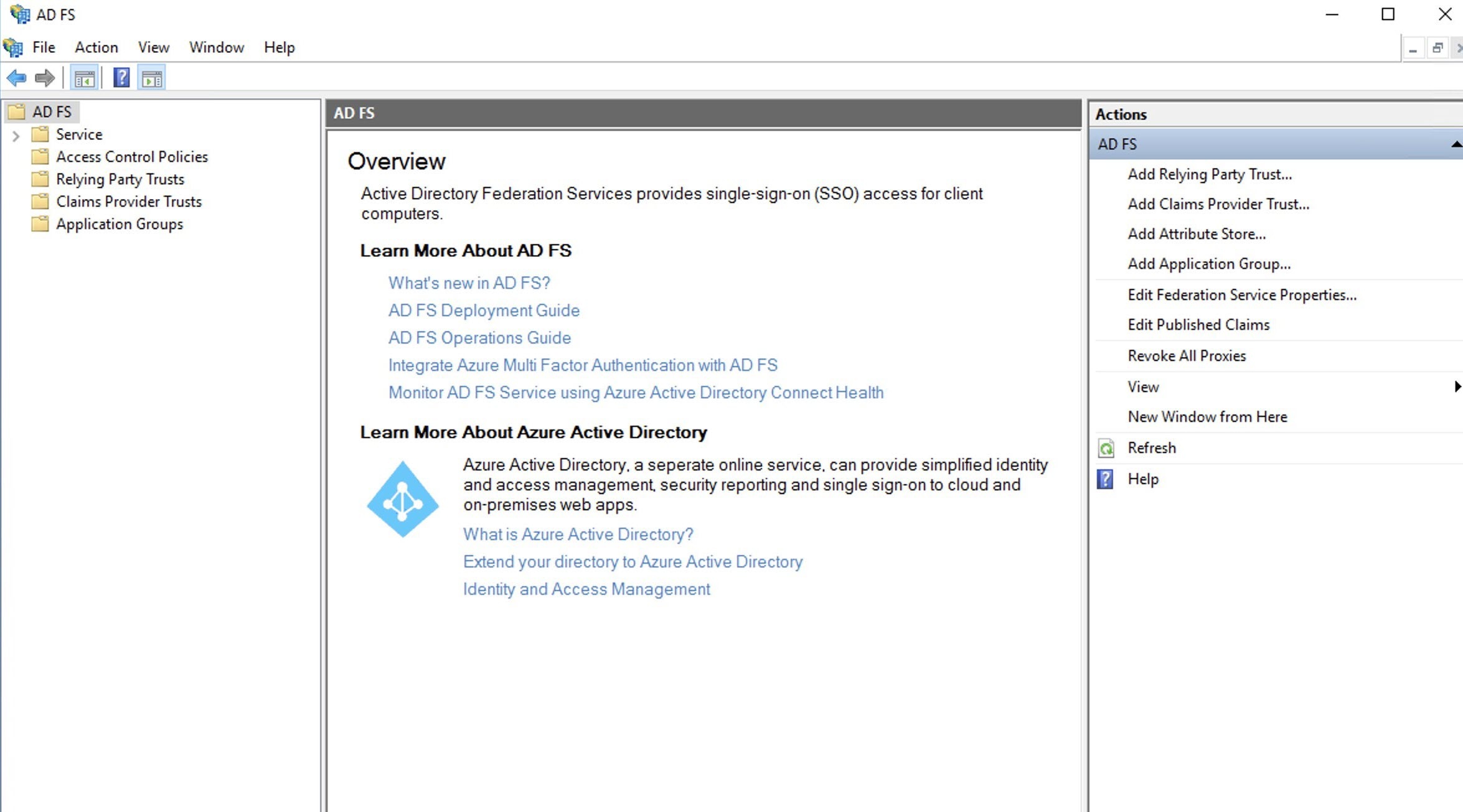
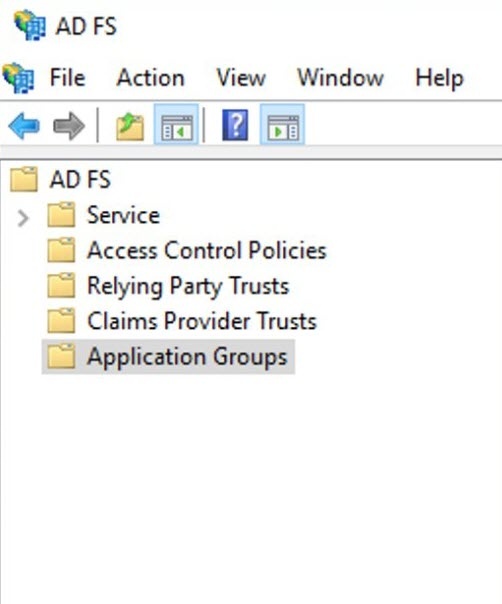
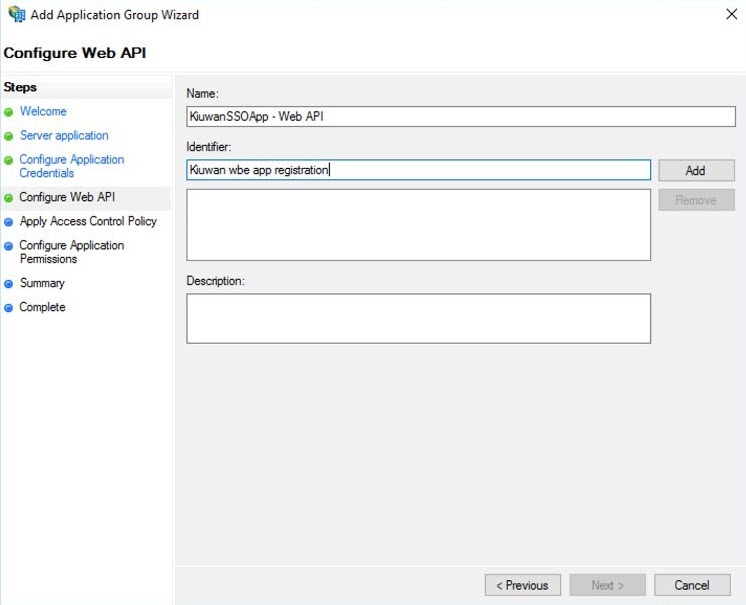
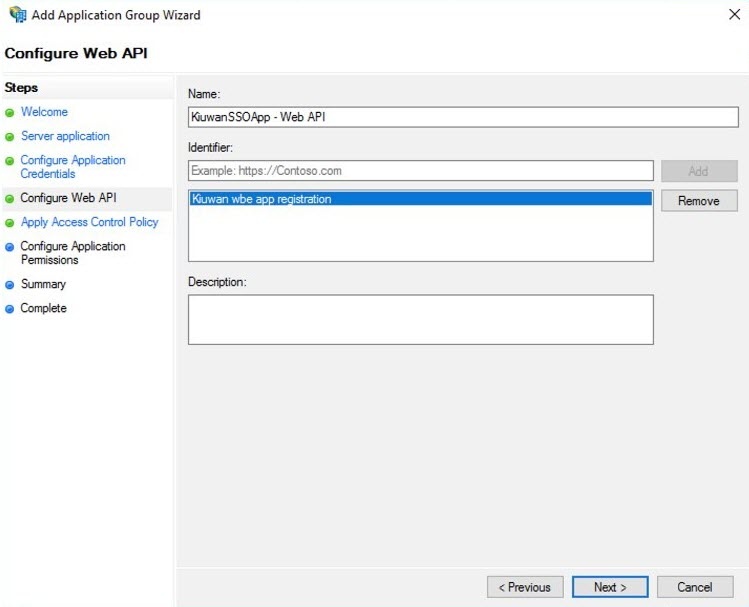
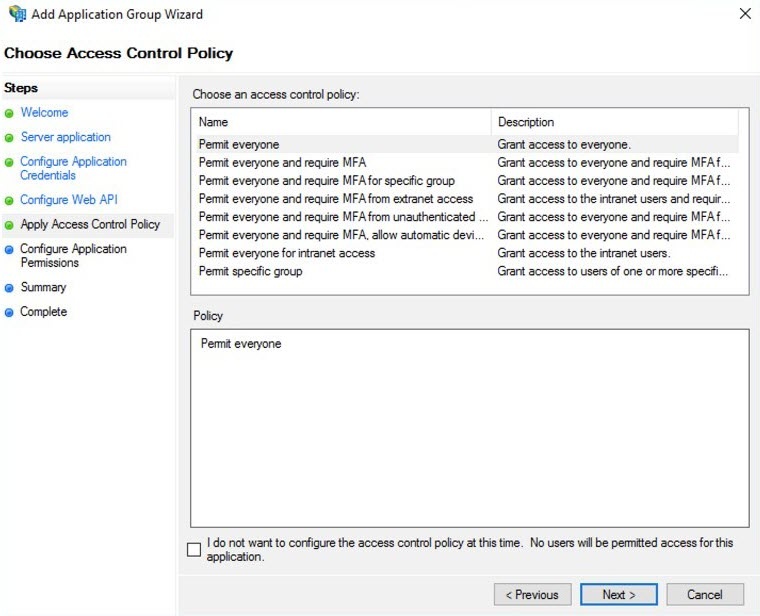
Similar to Azure DevOps, as with any other OAuth/OIDC issuer or identity provider, the configuration of ADFS follows the specifics defined for that Idp. However, information needs to be collected during the setup of Kiuwan as a registered app, as detailed in section Summary:
The process of registering Kiuwan as an OAuth/OICD application is straightforward.
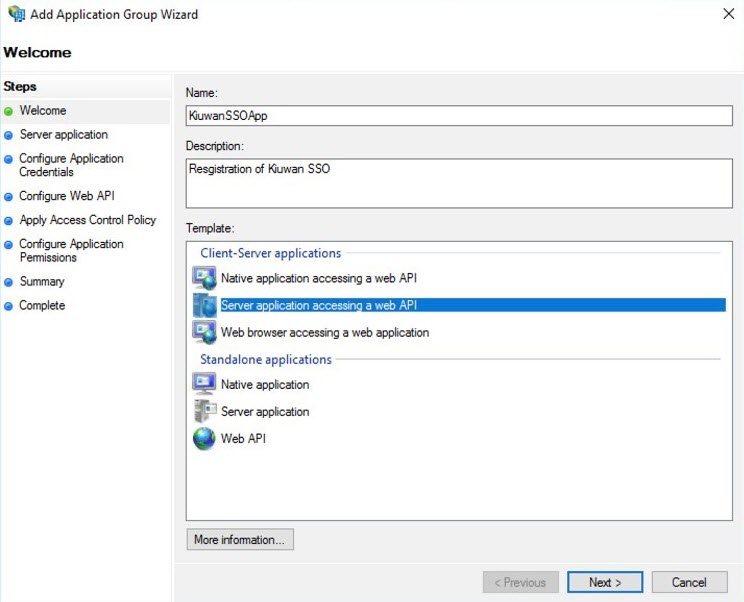
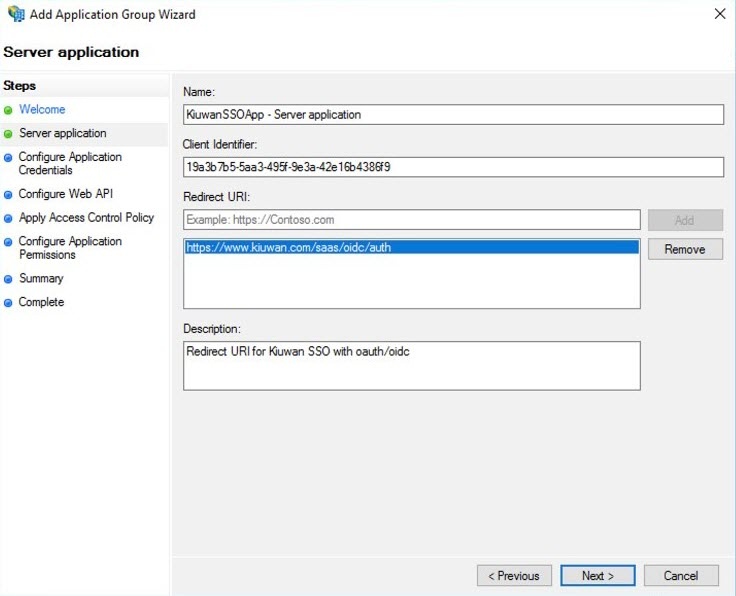
On the Configure Application Credentials tab, check the option Generate a shared secret, this will create the corresponding secret to be copied into the Kiuwan OAuth configuration panel, as described in Setting up Kiuwan SSO with OAuth/Open ID Connect. Click Next.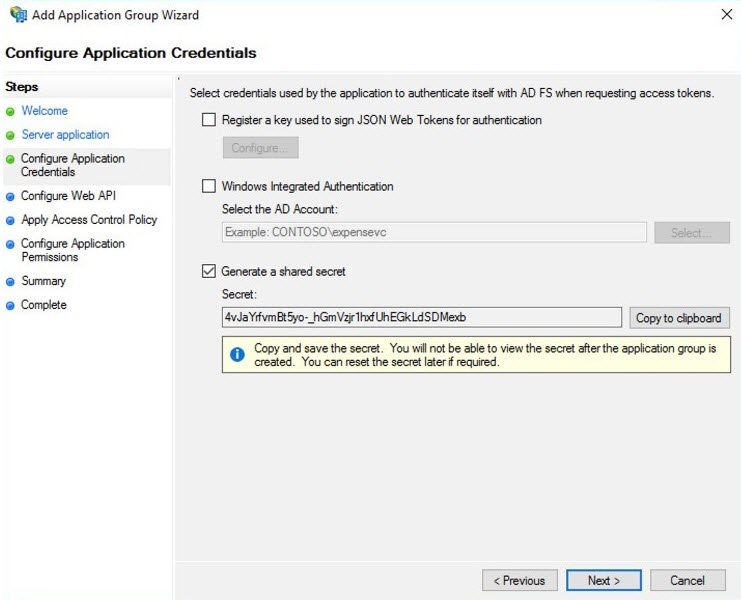
Copy the generated the shared secret for a temporary location as it will not be available again, and if needed it will need to be regenerated. |
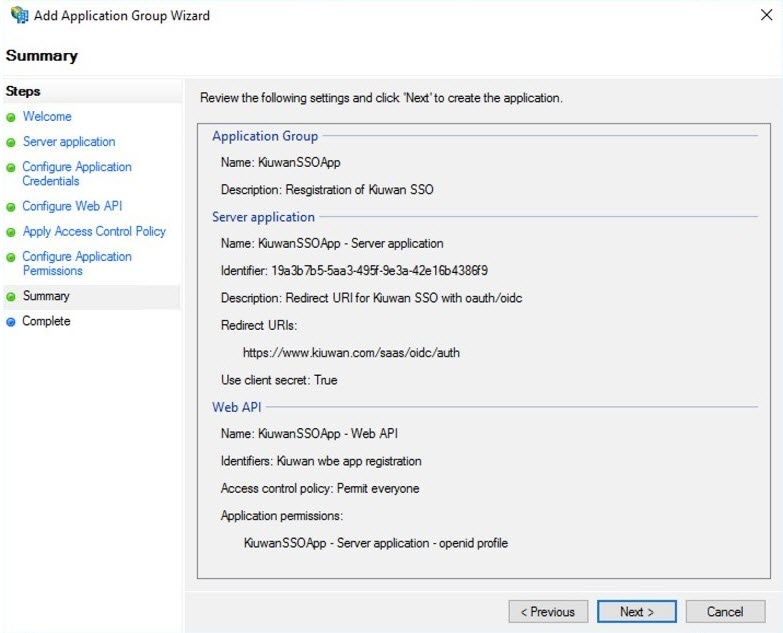
As stated, the application group and corresponding client are now configured.
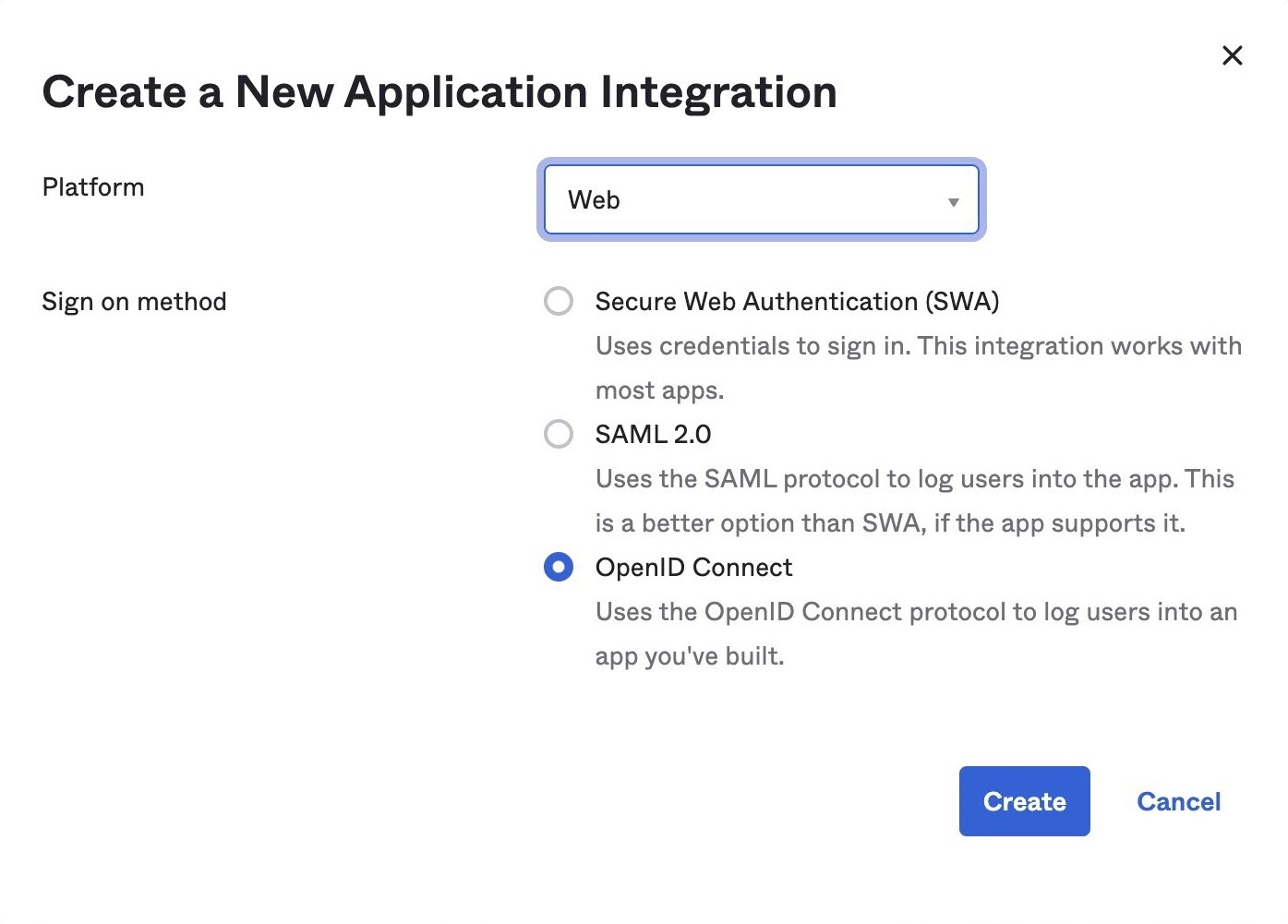
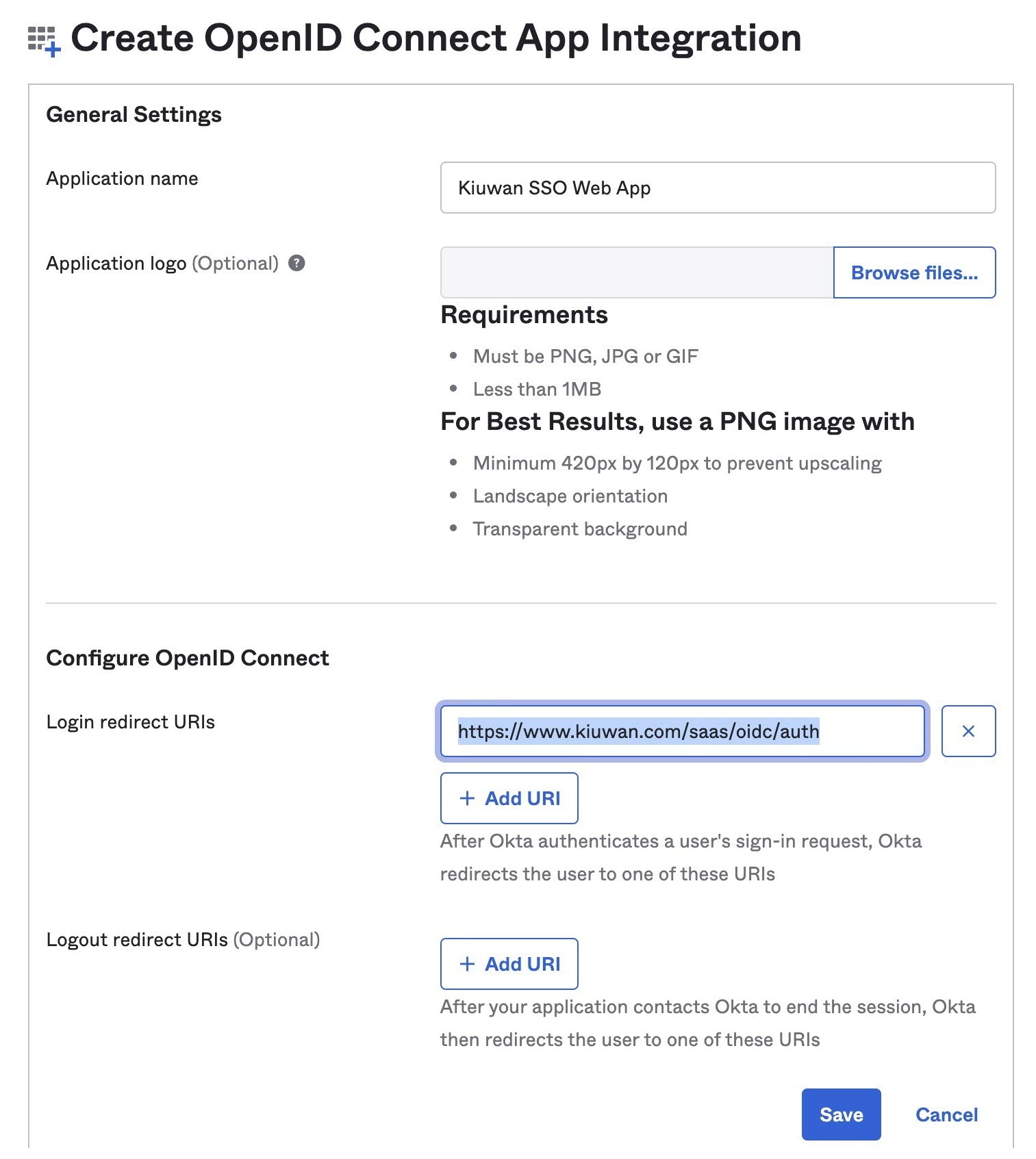
To use OKTA as an OAuth SSO identity provider, it is required to register Kiuwan in OKTA.
Follow these instructions to register Kiuwan in OKTA:
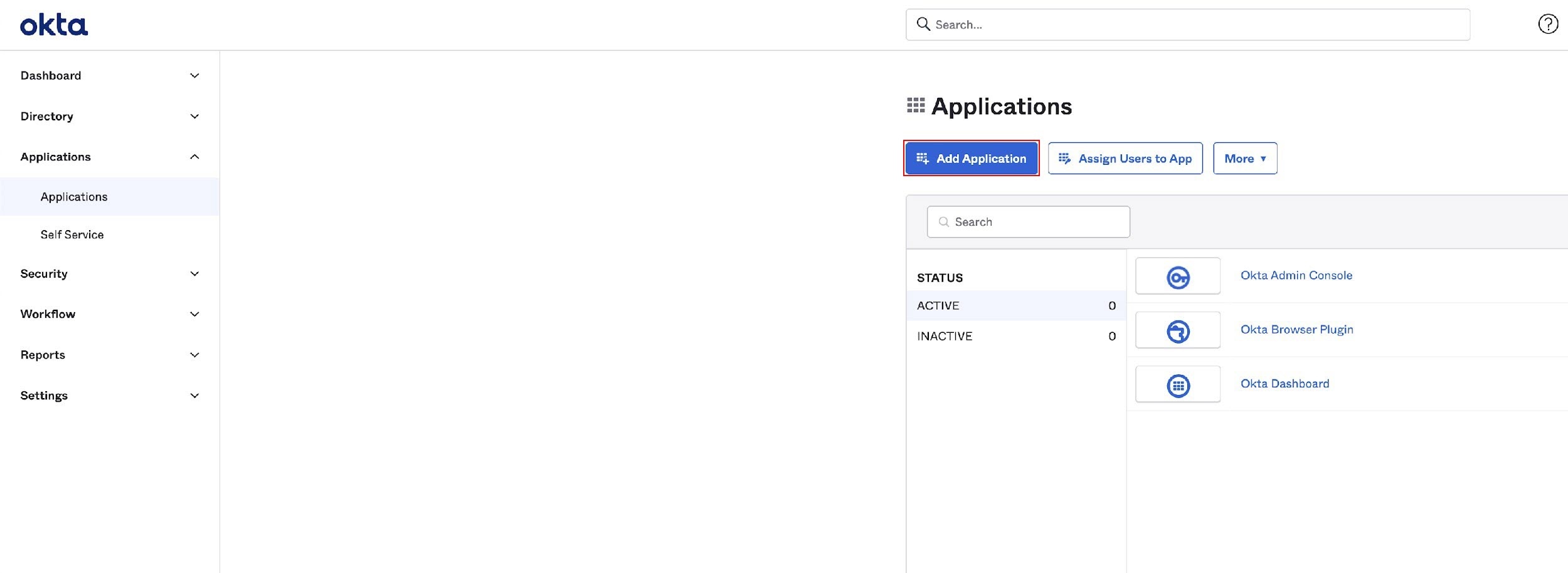
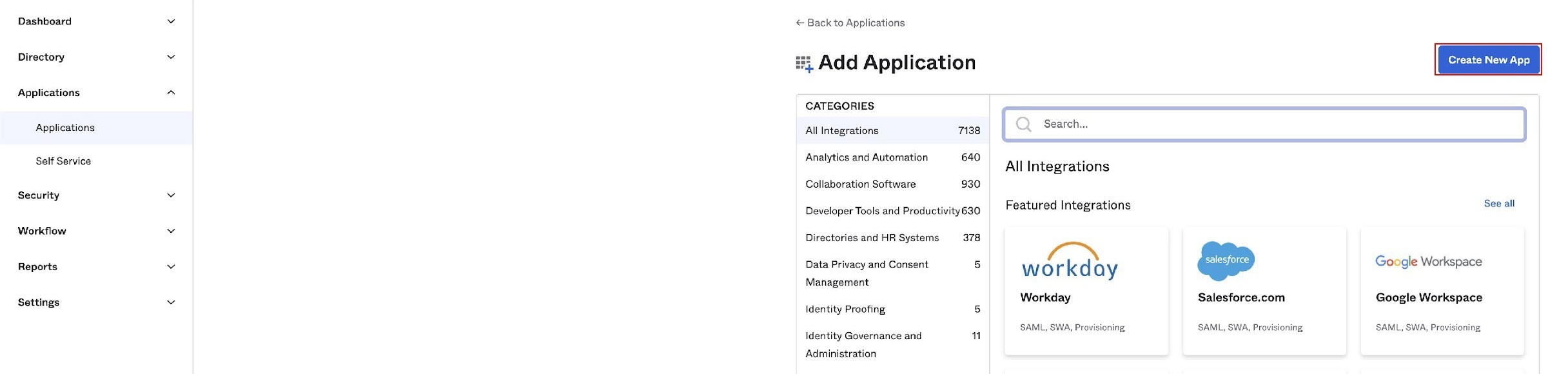
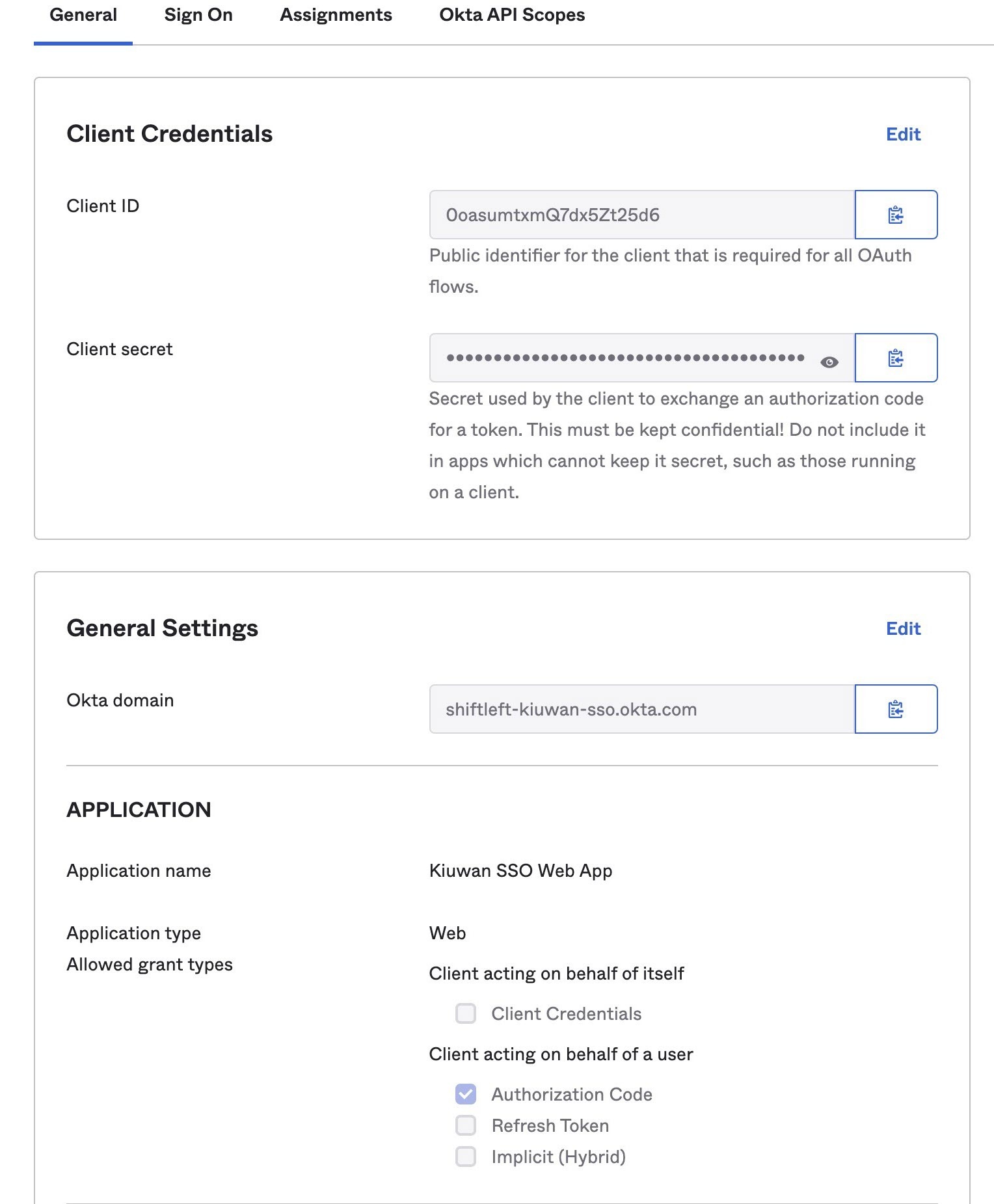
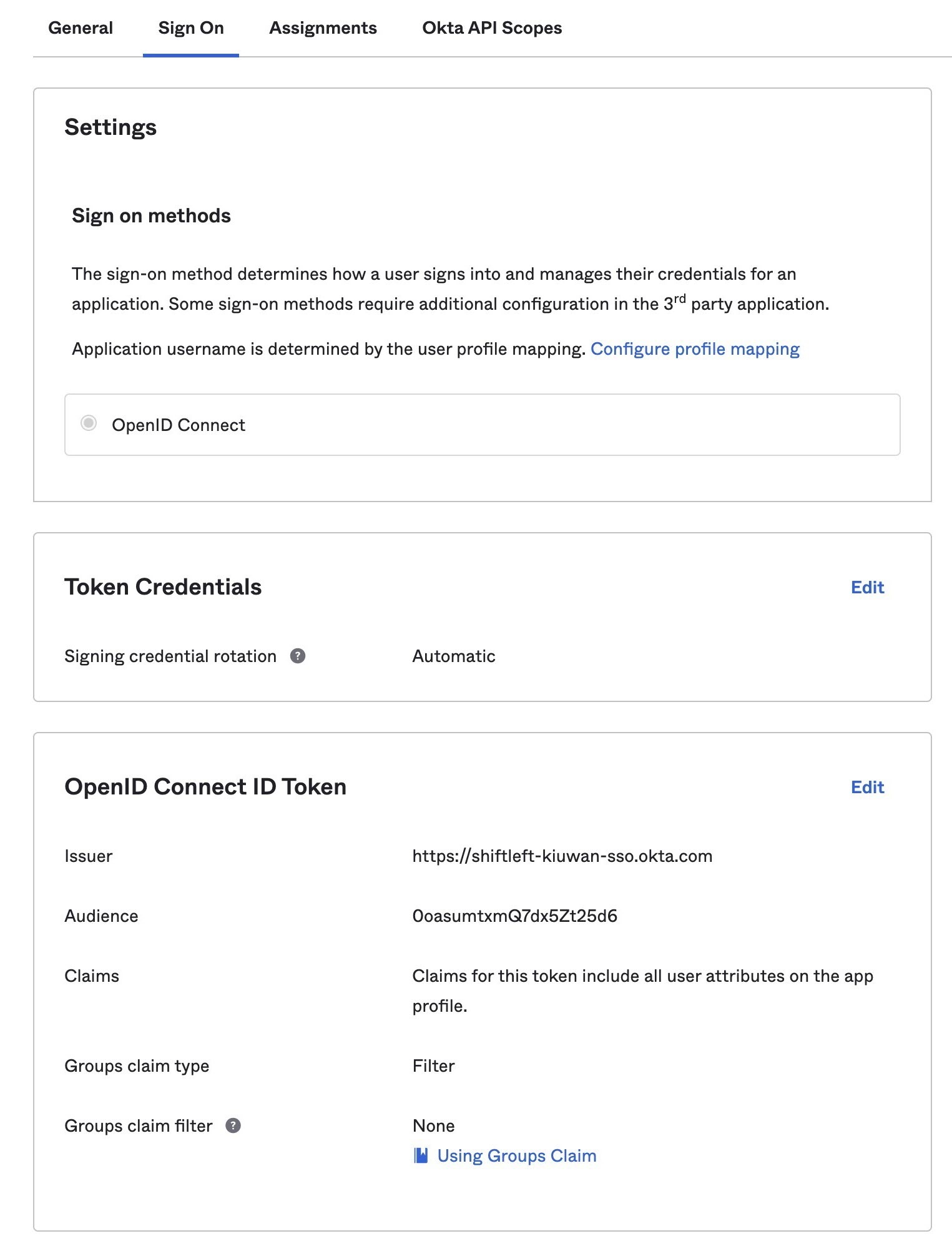
OKTA allows for additional configuration and provides extensive support, make sure you tailor the configuration to your needs.
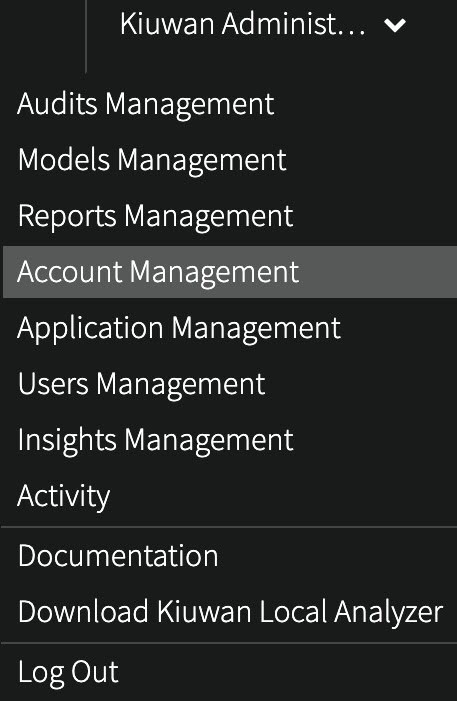
To set up Kiuwan SSO with OAuth/OpenID connect follow these instructions:
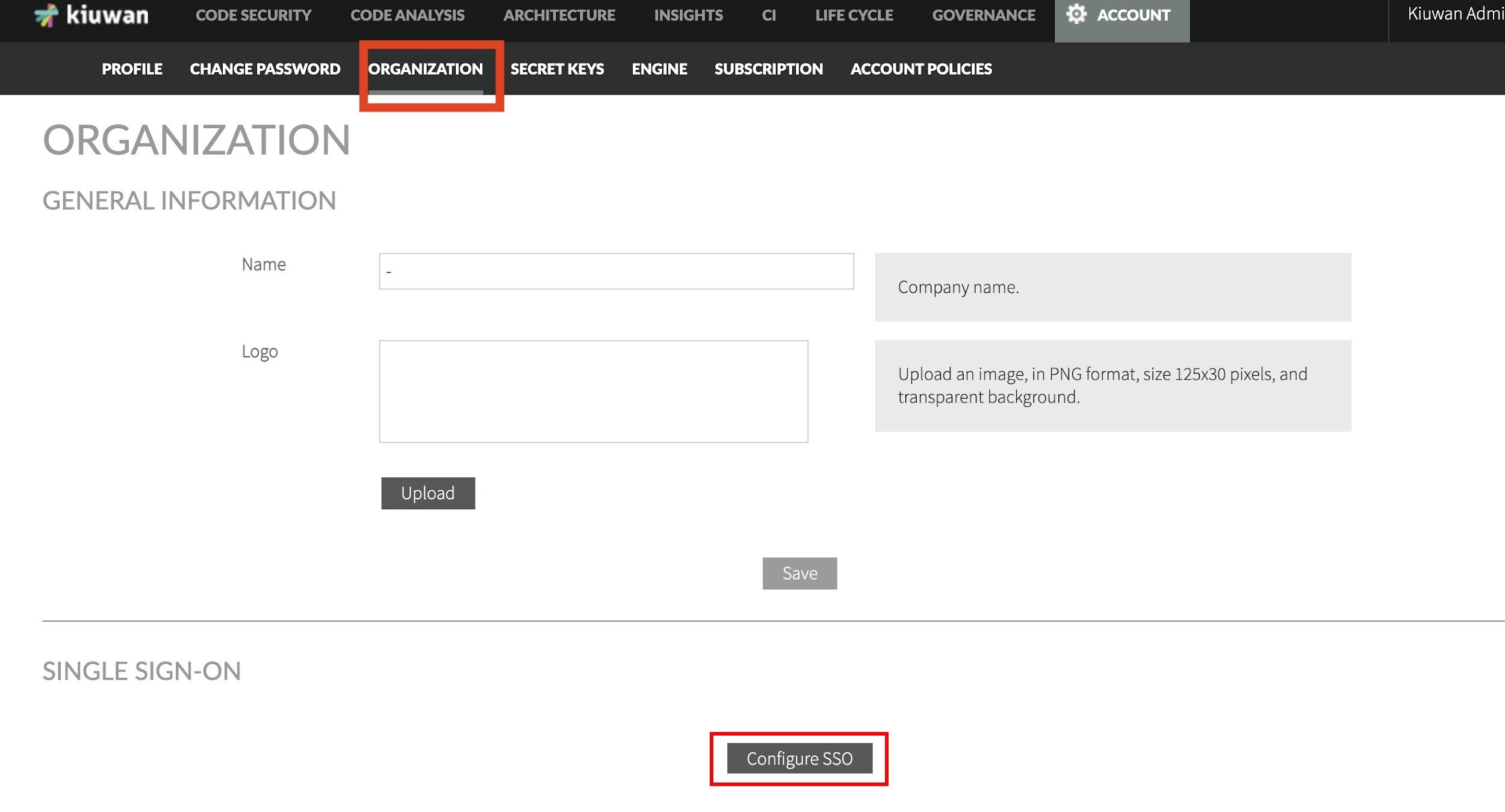
Select OAuth2/OpenID Connect option and confirm.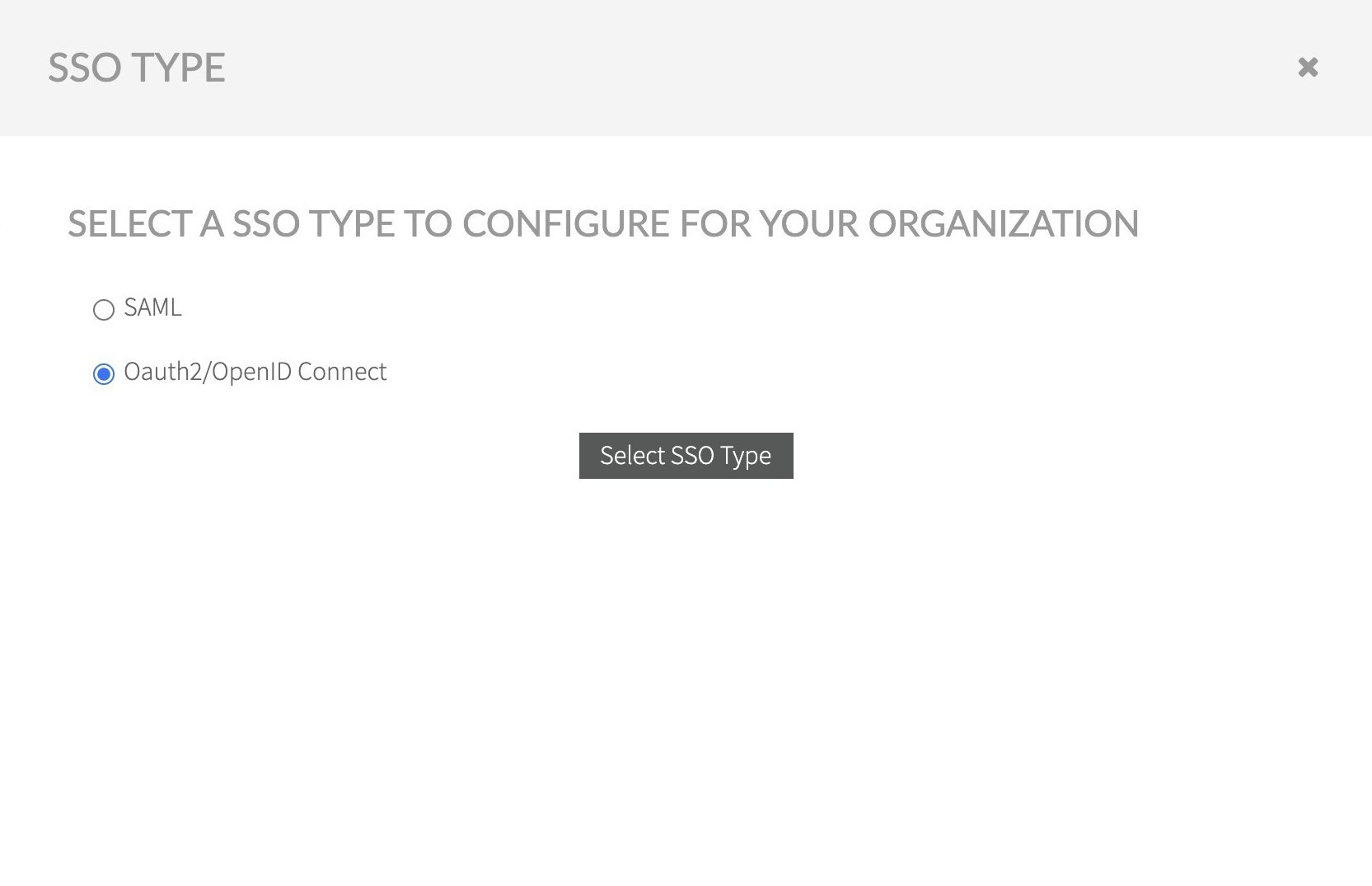
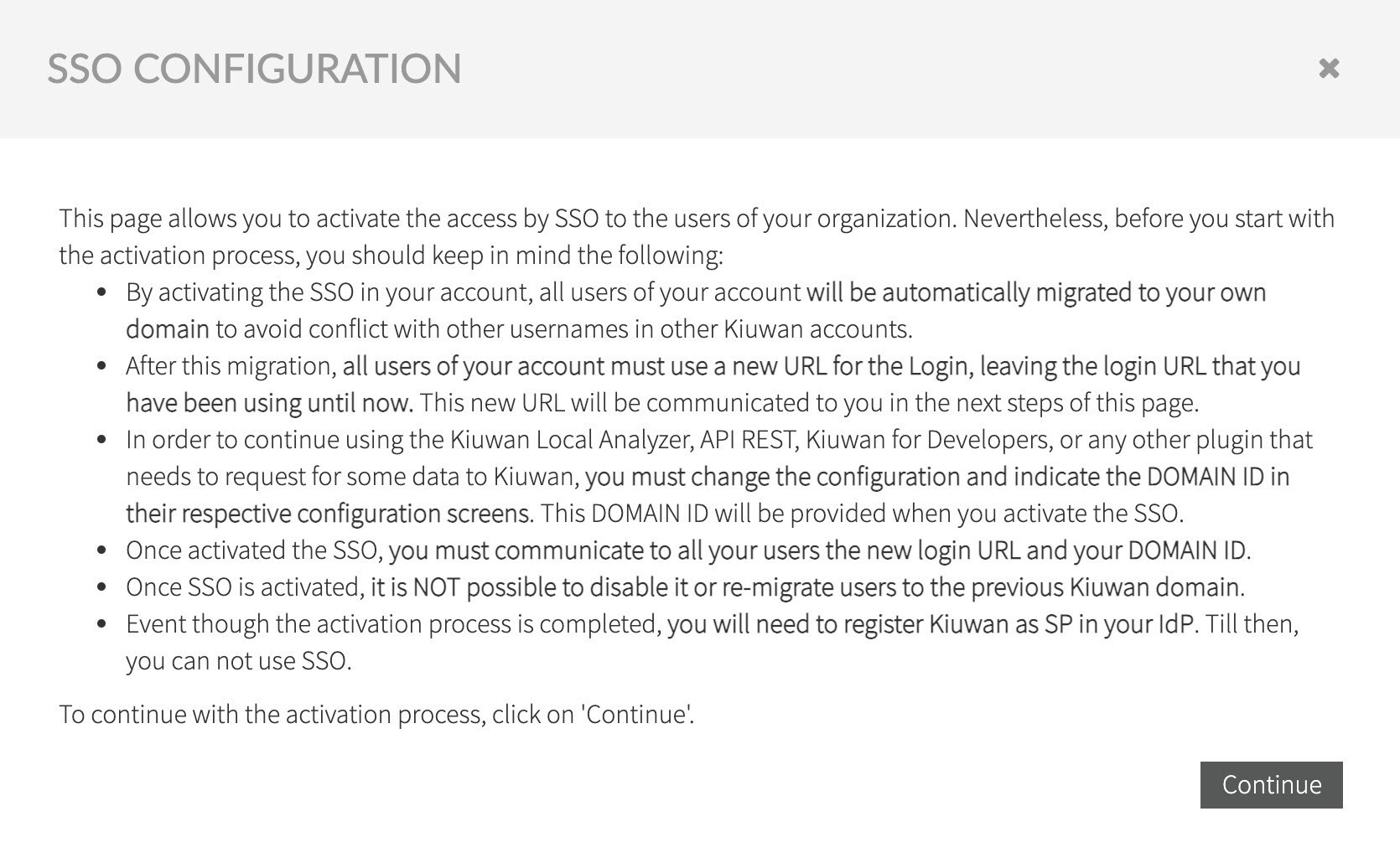
Read the following text explaining the implications when activating SSO, click Continue to proceed to the OAuth2/OpenID Connect setup.
Fill in the information, as gathered during Configuring OpenID Provider, and confirm entered data by selecting Enable new IdP.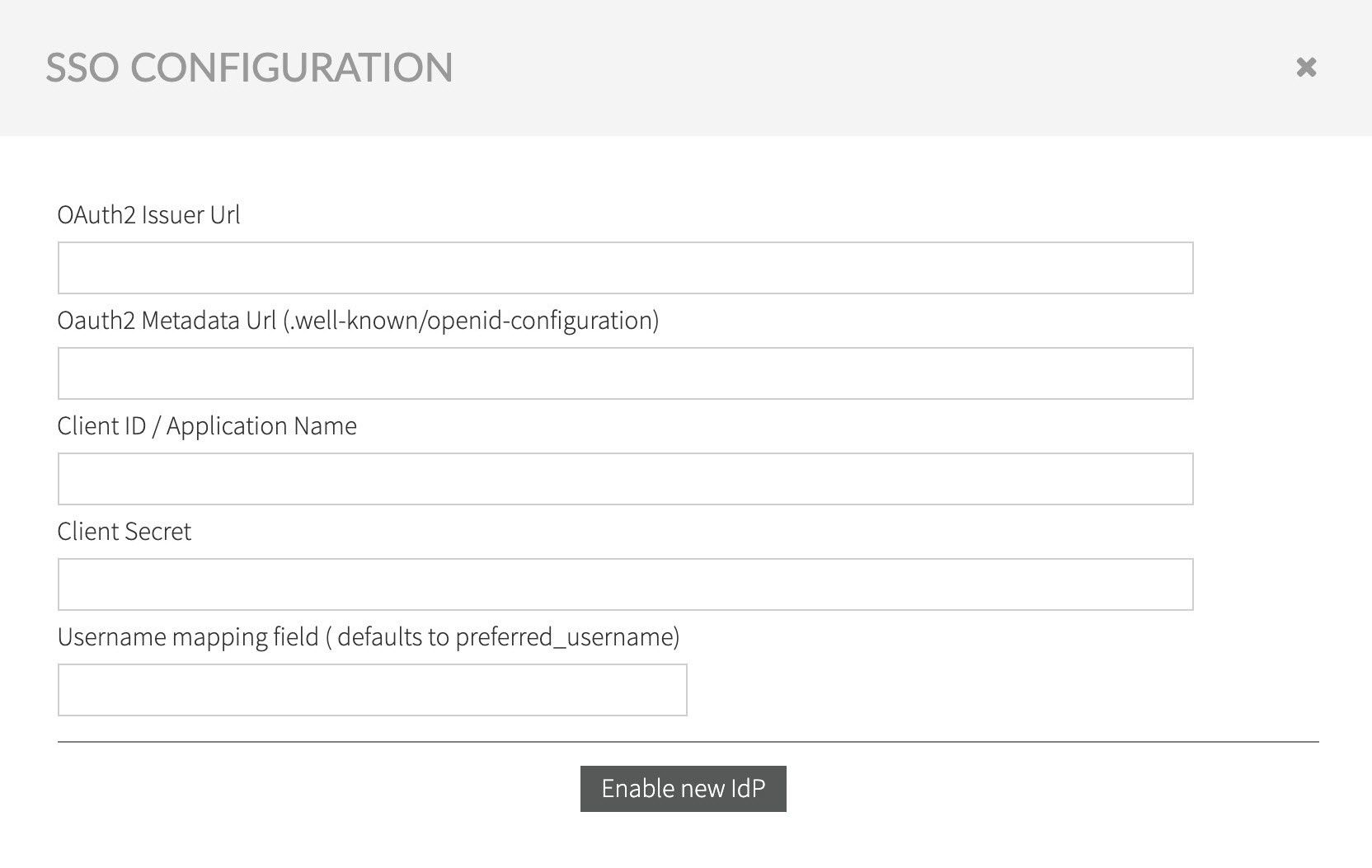
After confirming the SSO data, a new email is sent with the activation confirmation code, alongside the instructions explaining how to log in to Kiuwan after the SSO is activated.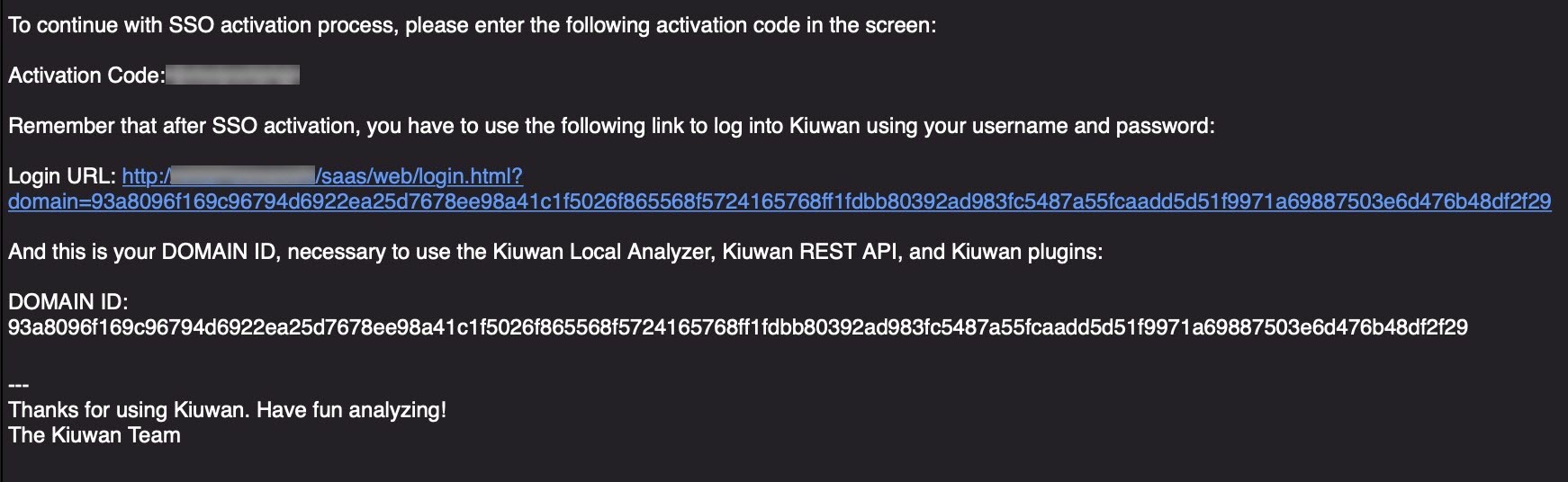
Copy the confirmation code and enter it in the confirmation form.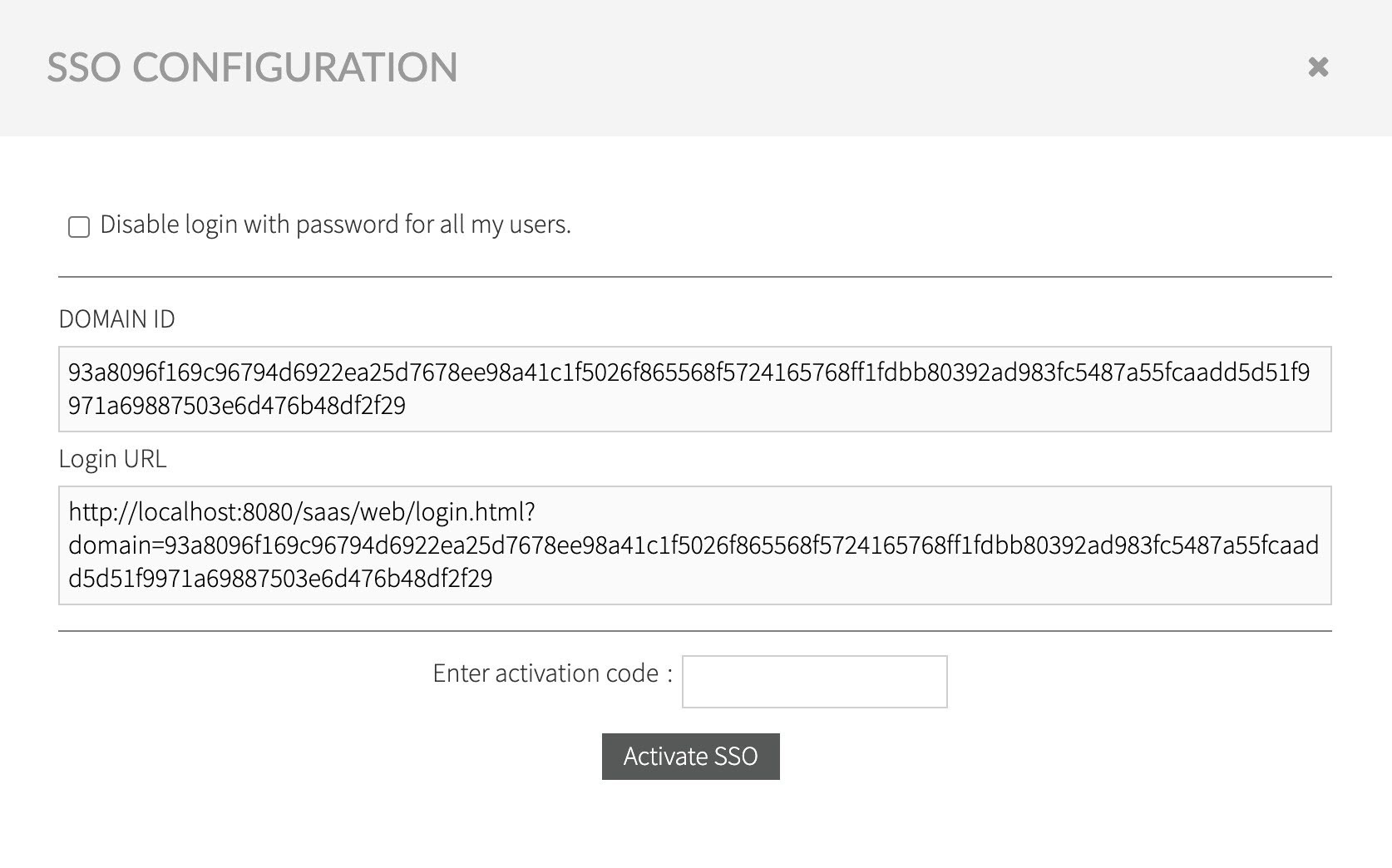
When the option Disable Login with password for all my users is checked, it prevents any user registered in your account, with the exception of Account Owner user, to be able to login using Kiuwan managed identity username/password. Users will be able to log in only through defined OAuth/OIDC server authentication. |
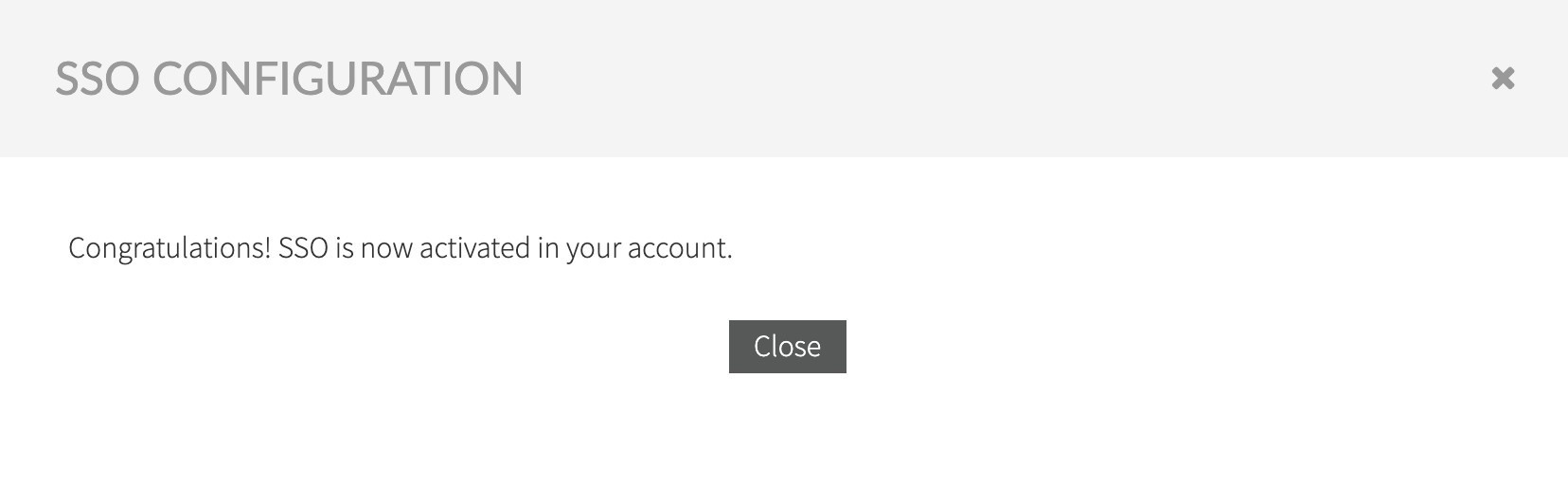
After entering the activation code a confirm the activation of SSO, the following confirmation dialogue displays:
As explained in the confirmation email received during the configuration process, and as shown, after SSO setup in the Organization tab in the Account Management section, after SSO is completed the login must comply with the following URL:
https://<kiuwan.server.url>/saas/login?domain=<the.created.domain>&sso=on
This link opens the following page, click login to redirect the user to the configured authentication page at the OAuth/OIDC identity management system.
Successful authentication will enable access to Kiuwan, with the corresponding authorization configured for the logged-in user.
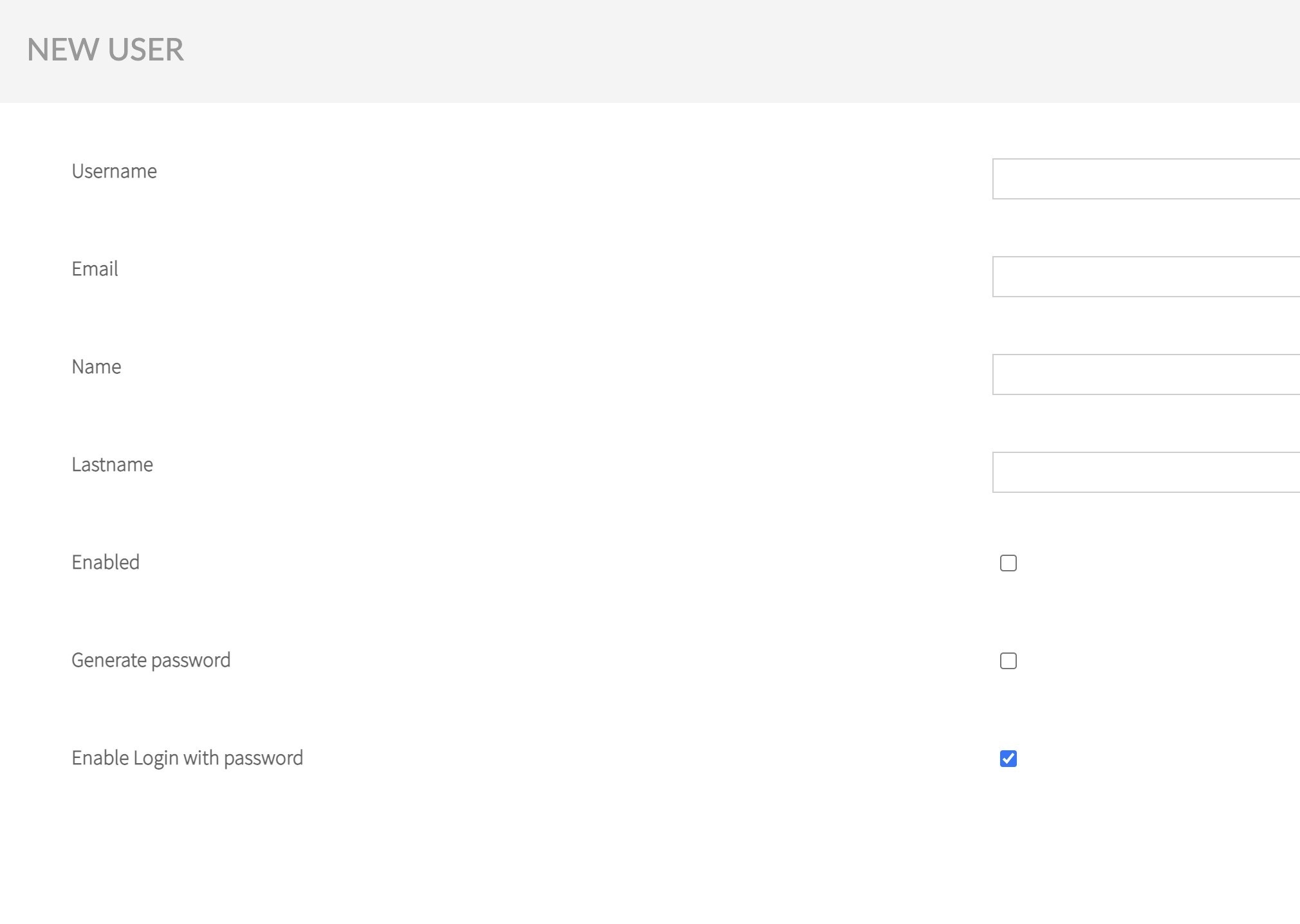
When the user is configured to login with Username and Password in Kiuwan, as shown below:
It is possible to login into Kiuwan bypassing the SSO, this is particularly useful for accessing Kiuwan through the provided REST API, or when SSO is unavailable. To do so, use the following construct to access the Kiuwan console application:
https://<kiuwan.server.url>/saas/login?domain=<the.created.domain>&sso=off
It opens the standard Kiuwan Login screen:
In either case, after setting up SSO, the domain must always be set during the authentication process, otherwise, Kiuwan will not be able to identify the corresponding user.
After an account is configured to use SSO through OAuth2, this configuration becomes also available to KLA.
To enable KLA to use OAuth2/OIDC in the login form follow these steps:

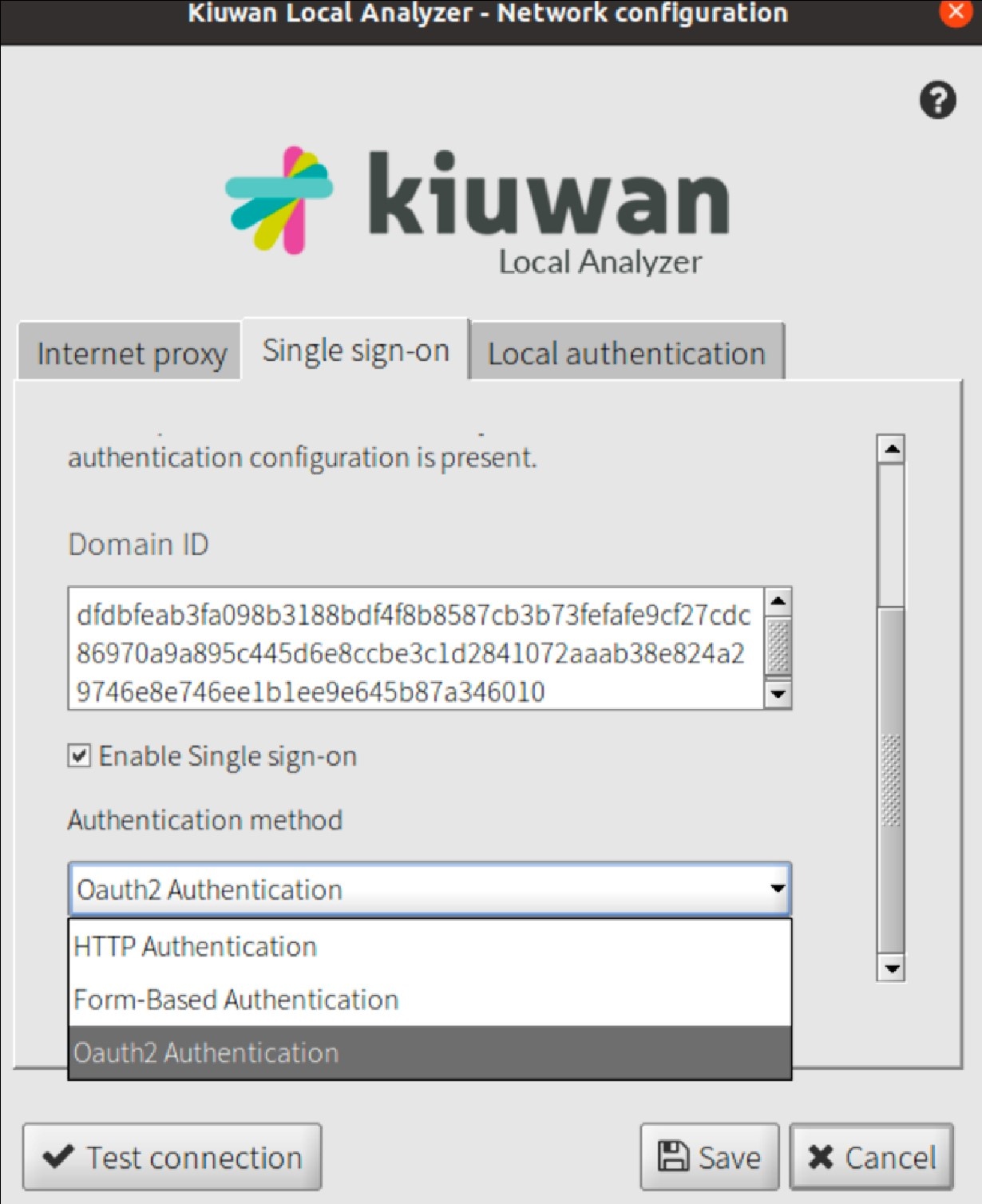
Click Test Connection and KLA will redirect the authentication procedure to the native web browser: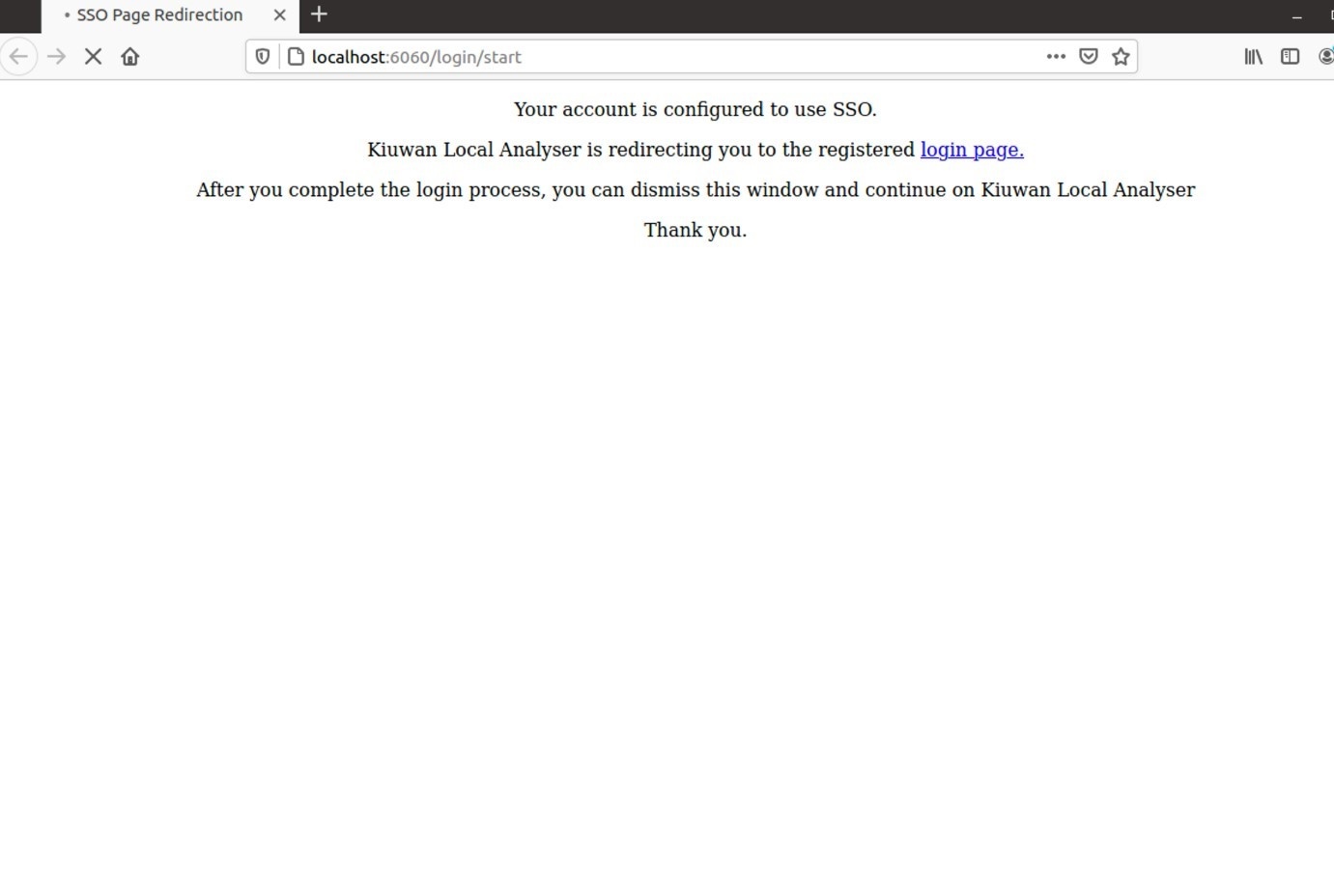
The above page is temporarily presented informing the user that the login process is underway, and finally the regular authentication process for the configured Identity provided is initiated.
After the authentication process is completed, the browser window can be discarded as KLA has collected the needed information to proceed.
When KLA is configured to use SSO with OAuth, the Login form will show an indication that SSO is activated.

By selecting Login in the login form, KLA starts a new browser window to initiate the login flow.
Initially, the browser displays the following information:
Eventually, it would be redirected to the regular Authentication page of the configured Identity provider for the selected account.
Upon successful completion of the authentication process, the browser window can be dismissed, and KLA will be available to be used according to the user's corresponding capabilities.