Vulnerabilities provide a detailed view of all the application’s vulnerabilities, allowing to:
- Search vulnerabilities according to multiple search criteria
- Order and group vulnerabilities by different characteristics
- Inspect details of every single vulnerabilities
- Access to vulnerability description and remediation tips
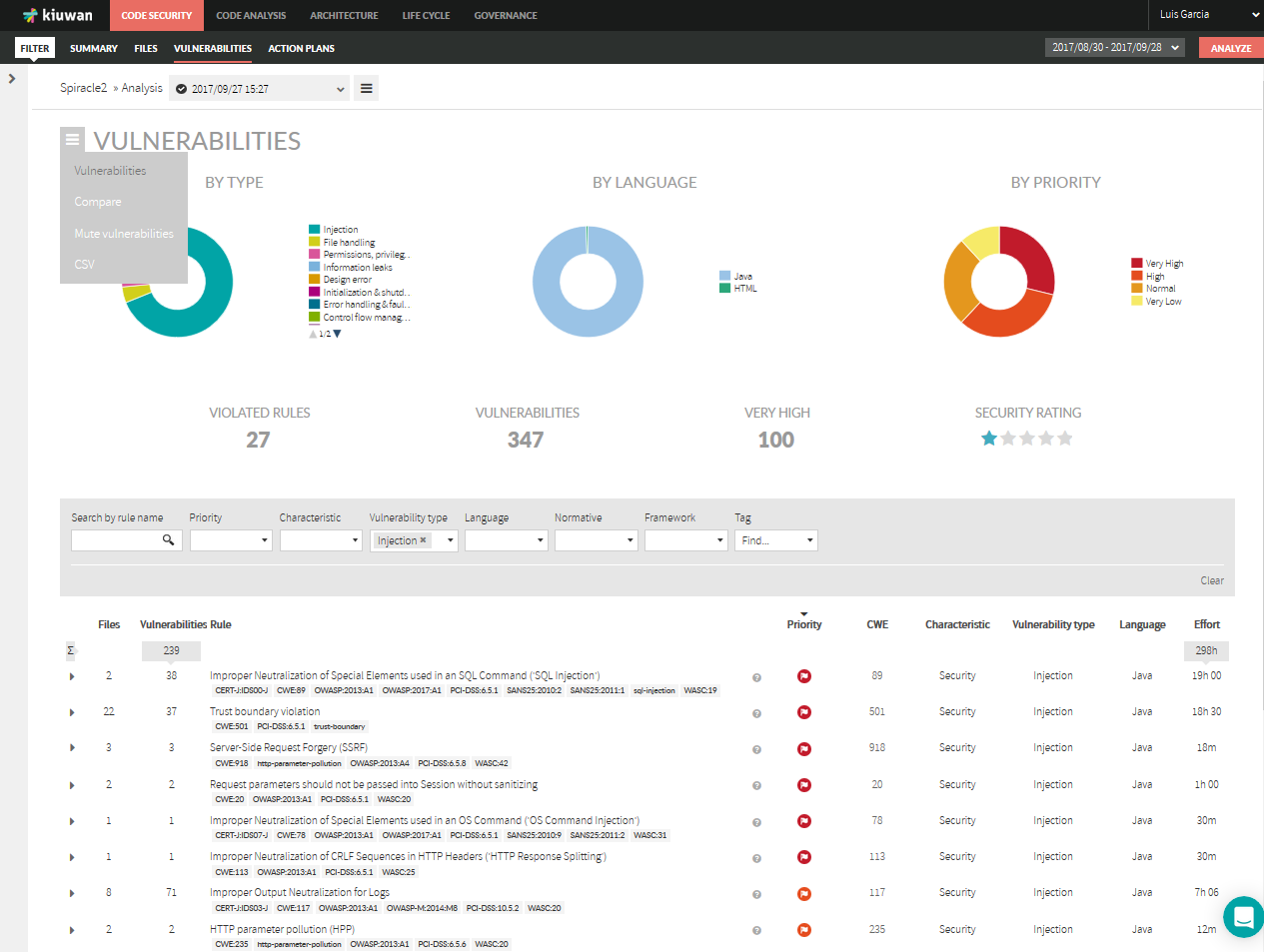
Summary data
Summary section displays group information on vulnerabilities:
- By Vulnerability Type: number of vulnerabilities for every type (please see Vulnerability Types )
- By Language: number of vulnerabilities found for every programming language
- By Priority: number of vulnerabilities found by priority (according to security rules priorities as defined in the model used for the analysis)
Figures are also displayed for
- Violated Rules: number of security rules (checks) with associated vulnerabilities
- Vulnerabilities: total number of vulnerabilities found in app source code
- Very High: number of Very High vulnerabilities
- Security Rating: overall application security rating
Clicking on the sandwich menu on the top-left you can:
- Compare analysis results with any other analysis
- Mute vulnerabilities
- Export vulnerabilities to CSV format
Please Kiuwan Code Analysis site for info on the above functionalities.
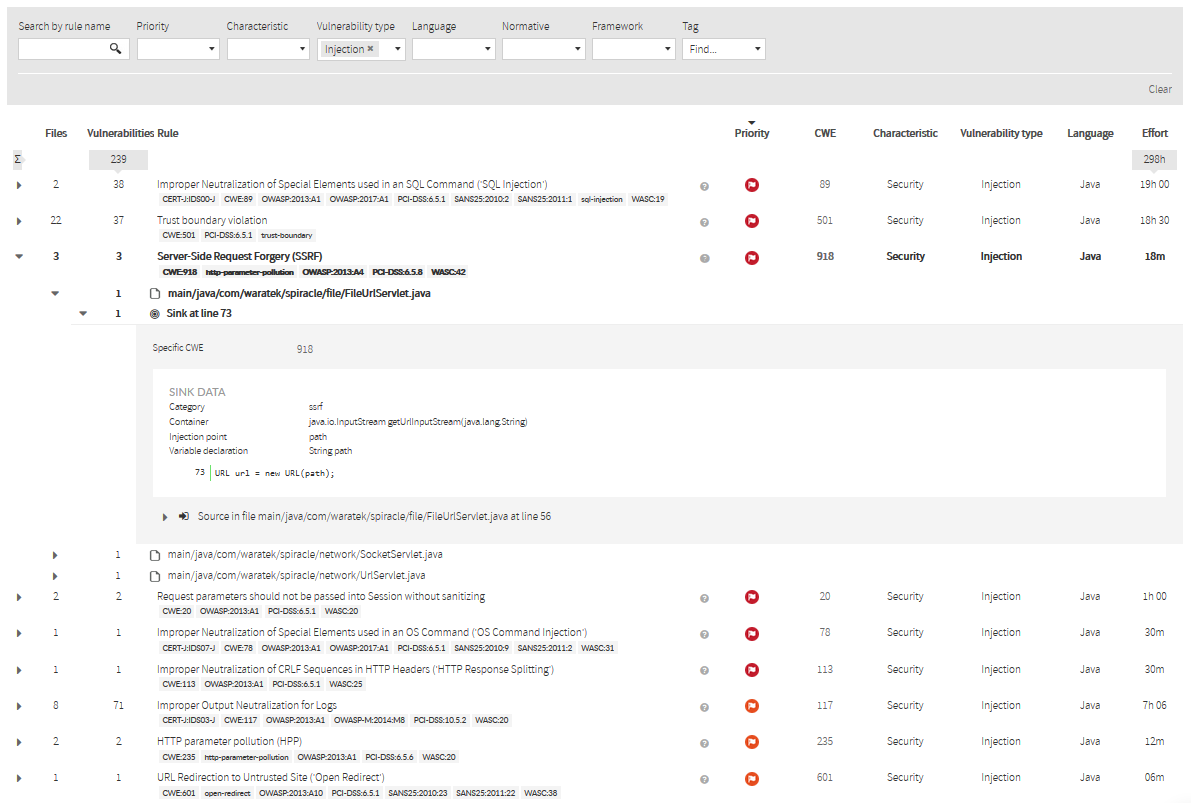
Detailed data
Along with these metrics, Vulnerability page displays a full listing of defects that you can browse, filter and order by following criteria:
- Files: Number of files that are not conformant to the selected security rule
- Defects: Number of vulnerabilities found for the selected security rule
- Rule: Name (desc) of the security rule
- Priority of the rule (from Low to Very High)
- CWE weakness reference(s) mapping for the selected security rule
- Characteristic : main software analytics categorization of the selected rule
- Vulnerability Type: security topic addressed by the selected security rule
- Programming Language
- Effort to invest to fix all the vulnerabilities of the selected security rule
Clicking on a vulnerability row will let you drill down to detail on security rule (from general description to the specific line of the vulnerability in a source file).
For further info, please visit Understanding Data-Flow Vulnerabilties