Introduction
Today’s time-to-market imposes high pressure on releasing new versions of your application. Productivity becomes essential. And most of the times, you will incorporate external open source components that let you build new functionality very fast and with the minimum effort.
Open Source repositories provides huge amounts of software that lets you to build new applications very fast and robustly.
But not all are benefits; there might be also some drawbacks when using open source components.
First obvious question has to do with how much open source software is your application using.
Do you have a complete components inventory with all the 3rd party components being used by your software?
If you are a developer you most probably know the answer to this question. But if you are in a position closer to management, it’s likely that you don’t know the answer.
Modern applications, in most of the cases, are using open source components and yours will not be an exception. And, although the benefits are clear, you might be thinking of some inherent risks .
Do you know the degree of security breaches introduced by using those 3rd party components?
You most probably are dedicating a lot of effort to remediate security vulnerabilities in your software, but those efforts are useless if 3rd components are vulnerable. As you know, any security vulnerability makes the whole application vulnerable.
Are those components obsolete? You might be using “outdated” components or, even worse, “dead” components..
What if you are using old versions of those components? Old versions might be introducing security breaches or bugs that are solved in newer versions.
Or even worse, what would happen if those buggy components are dead, i.e. are not being evolved?
Are you aware of legal licensing implications of using those 3rd party components?
There are many 3rd party components that are “Copyleft” licensed.
In a broad sense, this kind of licenses means that, although you are allowed to use that software in your application, once you have included in your application, the whole application becomes “Copyleft” licensed, i.e. you are implicitly giving every person who receives a copy of your software permissions to reproduce, adapt, or distribute it.
Is this your intention? If don’t, you should identify all Copyleft’d components you are using in your application and act accordingly.
These, and probably others, are common questions when using 3rd party components.
Kiuwan Insights
Kiuwan Insights comes to answer all these questions by providing:
- a complete Components Inventory of 3rd party software used by your applications, and
- detailed information on Security, Obsolescence and Licensing Risks of those components
At a glance, Kiuwan Insights provides visual indicators that quickly let you to know the different levels of risk associated to every external component.
Every component is assigned a level (High, Medium, Low or None) on three different risk metrics:
- Security Risk (due to vulnerabilities introduced by components)
- Obsolescence Risk (due to using obsolete components)
- License Risk (due to legal implications of used components’ licenses)
Components Inventory
If you are a developer, you most probably will access to build systems where external components are “identified”.
But, are those 3rd party components part of a “controlled” inventory? Most probably, don’t.
Kiuwan Insight analyzes your application software, discovering all external dependencies, and builds a Components Inventory that lets you track of any external piece of code that could be part of your application.
Supported languages and resources
Kiuwan Insights uses the following resources to extract information on 3rd party dependencies.
Supported languages | Supported repositories | Supported build systems |
Java |
|
|
Javascript |
|
|
.Net |
|
|
Python |
|
|
Swift |
|
|
Php |
|
|
From these sources, Kiuwan Insight builds the Components Inventory of your application.
Components Inventory is accessible trough Insights >> Components tab.
Insights >> Components
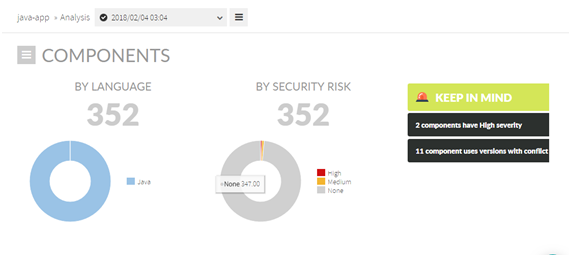
Insight >> Components tab displays Components Inventory:
- Overall Information on Components – aggregated information on number and type of components
- List of Components – detailed listing of components
- Component detail – detailed information on selected component
Overall Information on Components
- Number of components by language
- Number of components by Security Risk level (High, Medium, Low and None)
- Alerts :
- Components with High Security Risk
- Components being used with different versions that might be cause conflicts
- Etc.
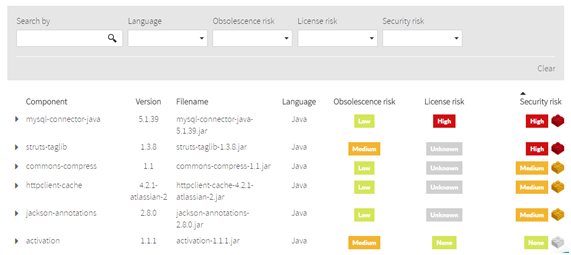
List of Components
Kiuwan Insights provides a full listing of all those components being used by your application.
For every 3rd party component, you will have access to detailed component information such as:
- Component name and description
- Used version(s)
- Its filename (i.e. physical container) (.jar, .dll, .js, etc)
- Programming language
- Obsolescence risk (see XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX)
- License risk (see XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX)
- Security risk (see XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX)
Security risk
Security Risk
A component’s Security Risk is based on CVSS v2 Base Scores (Severities) of its vulnerabilities:
- If the selected component has more than one vulnerability, Kiuwan will label the component with the highest severity value of all the vulnerabilities of the component.
- If the selected component has only one vulnerability, the Severity of that vulnerability will be the Security Risk of the component.
Please visit XXXXXXXXXXXXXXXXX for further information on CVSS v2 Base Scores (Severities) of vulnerabilities.
Obsolescence risk
Obsolescence Risk
A component’s Obsolescence Risk is a measure of the risk level relative to:
- the antiquity of your version respect to the latest version, and
- how active is the component
Both values are combined in the Obsolescence Risk to provide a value of the risk associated to using outdated or “dead” components.
Please visit XXXXXXXXXXXXXXXXX for further information on Obsolescence.
License risk
License Risk
A component’s License Risk is a measure of the risk level relative to legal implications of used components’ licenses.
Please visit XXXXXXXXXXXXXXXXX for further information on Licenses.