AppSec Blog
Keep up with the latest news on cybersecurity, technical trends, and programming best practices.
Do Your Apps Use Third-Party Components? Scan Your Code
Many software projects incorporate third-party components to add specific functionality. One of the biggest problems IT teams face is keeping up with what’s being used. Without a rigorous framework...
What Code Security Risks Exist Beyond OWASP Top 10?
The OWASP Top 10 is a great starting point for mitigating code security risks. However, businesses that want to be prepared for modern cyber threats must go beyond a checklist of typical threat...
Shifting Left with Security: DevSecOps for Early Vulnerability Detection
Complacency and passivity are no longer options for app security. Today’s software build failures can become tomorrow’s headaches when hackers locate the vulnerabilities your company failed to...
Ensuring Mobile App Security in the Age of Hyperconnectivity
In 2021, the hyperconnectivity market was valued at $319.4 billion. By 2031, it’s expected to expand to a value of $2.2 trillion. In fact, according to Forbes, the motto of the future is...
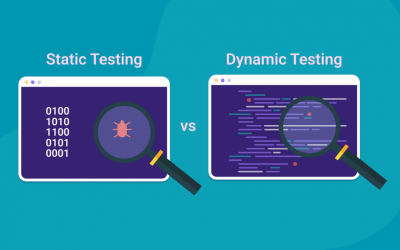
Your Guide to Static Testing vs. Dynamic Testing
As developers continuously push for quicker release cycles without compromising on quality, using effective testing strategies and tools are key factors in improving quality and efficiency. Code...
A Guide to SBOM Best Practices and Fundamentals
Organizations and developers who create and maintain software may have software bills of materials (SBOMs) but don't quite hit the mark when it comes to creating them. Sure, they know SBOMs are...
The Importance of Open-Source Scanning
When almost every application uses multiple open-source elements, securing your open-source code is more important than ever. However, open-source scanning doesn’t have to be a hassle. Discover why...
5 Reasons to Check Code for Vulnerabilities Before Shipping
Code vulnerabilities are among the leading causes of data and security breaches, alongside human errors. This is because, at the beginning of software development, developers often focus more on...
How to Choose the Best SAST Tools
The scope and number of cyber threats facing developers are growing every day. It’s vital for companies to adopt robust security measures to safeguard their sensitive data and mitigate the risk of...
How to Choose Code Scanning Tools
For as fast as the software development process can go, it’s all too easy for application security to become an afterthought. However, the right code scanning tools can make app hardening an organic...
How to Prevent Reverse Shell Attacks
Reverse shell attacks are one of the most common threats businesses have to face today. Even more, hackers are getting better and better at using them to compromise your organization’s security and...
Best Practices for Source Code Security
Following these source code security best practices allows your developers to protect your application from reverse engineering attacks.